We are thrilled to announce the availability of Calico Enterprise 3.5, which delivers deep observability across the entire Kubernetes stack, from application to networking layers (L3–L7). This release also includes data plane support for Windows and eBPF, in addition to the standard Linux data plane. These new capabilities are designed to automate, simplify and accelerate Kubernetes adoption and deployment. Here are highlights from the release…
Application-level security and observability: Get the benefits of a service mesh, minus the operational complexity
The majority of operational problems inherent to deploying microservices in a distributed architecture are linked to two areas: security and observability. At the application level, the need to understand all aspects associated with service-to-service communication within the cluster becomes paramount. DevOps teams often struggle with these questions: Where is monitoring needed? How can I understand the impact of issues and effectively troubleshoot? How can I effectively protect application-level data?
If observability and security are your primary drivers for considering a service mesh, Calico provides L3–L7 observability and security without the additional overhead associated with a service mesh. Calico integrates Envoy at the node level to provide deep observability of microservices at the application level. Since HTTP is one of the most popular protocols for microservices communication, this integration gives operators access to new network flow logs for application-level traffic that include valuable metadata and metrics for analysis and troubleshooting. When combined with high-performance, data-in-transit encryption using WireGuard, this gives DevOps teams service mesh observability and security benefits, without the need to deploy a service mesh along with all of its operational complexity and performance penalties.
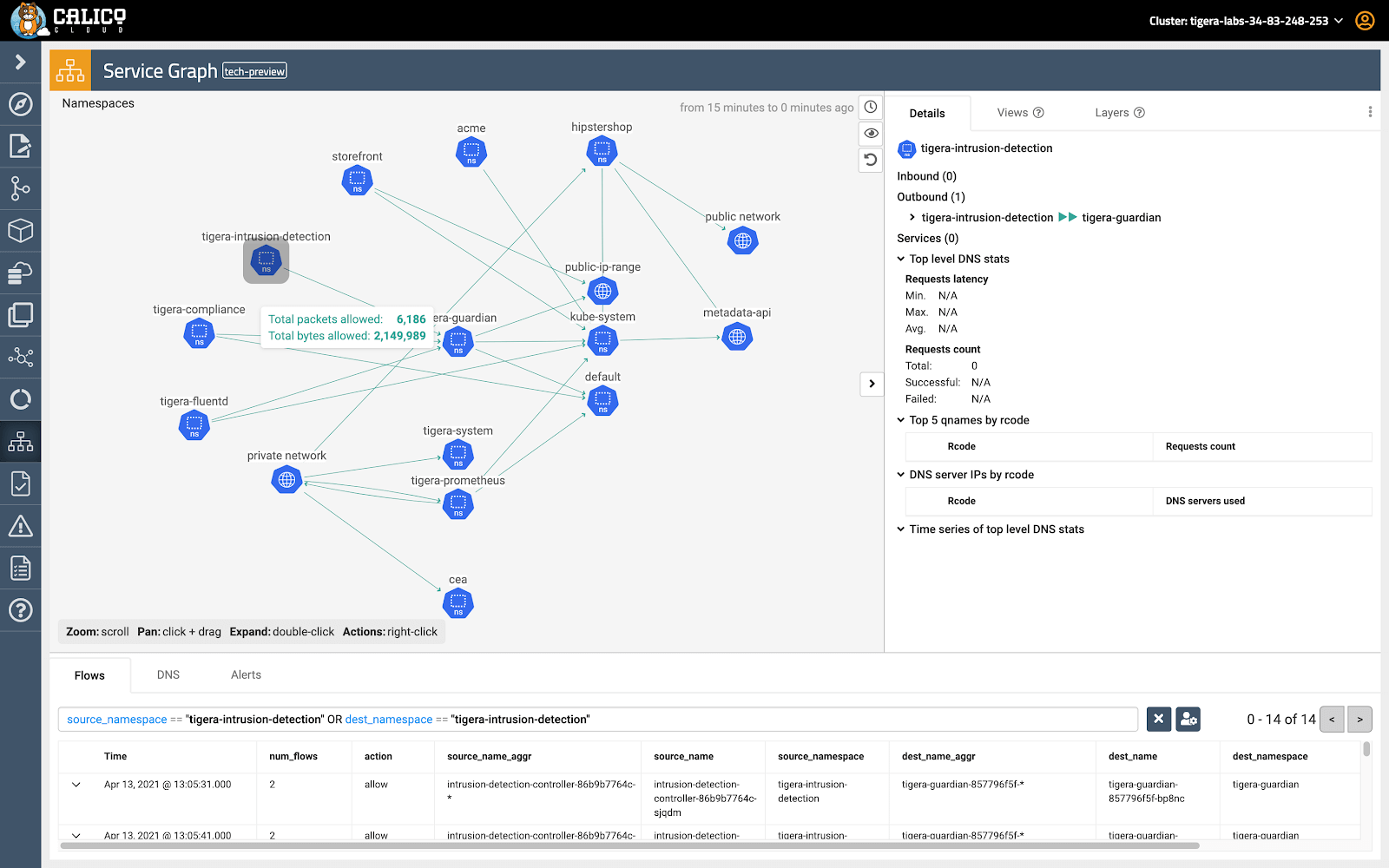
Dynamic Service Graph: Accelerating Kubernetes problem identification and troubleshooting
While development teams and service owners typically understand the microservices they are deploying, it’s often difficult to get a complete, shared view of dependencies and how all the services are communicating with each other across a cluster. Limited observability in a dynamic, distributed environment like Kubernetes makes it extremely difficult to troubleshoot and resolve end-to-end connectivity issues that impact application deployment. And downtime is expensive!
The Dynamic Service Graph available in Calico provides visibility across the stack from network to application layer (L3–L7) and provides the most accurate view of how services are operating in your Kubernetes cluster. It can generate a detailed visualization of the cluster environment that enables anyone to easily understand how microservices are behaving and interacting with each other at runtime, simplifying the debugging process. The graph provides DevOps, SREs and service owners with a point-to-point, topographical representation of traffic within a cluster that shows how workloads are communicating within the cluster, and across which namespaces.
Along with this information, the Dynamic Service Graph provides metadata on ports, protocols, how security policies are being evaluated, and other details that help Kubernetes teams understand how end-to-end communication is occurring. Performance hotspots are automatically identified and highlighted, and alerts are provided in the context of the graph. This feature also includes advanced capabilities to filter resources, save views, and troubleshoot DNS issues. The unique perspective provided by the Dynamic Service Graph’s expansive topographic view enables software engineers to quickly identify the source of a problem at the application, process, and socket levels as well as through an automated packet capture function.
Packet capture: Fast, automated ‘PCAP’ for Kubernetes
Packet capture (PCAP) is a valuable technique for debugging microservices and application interaction in day-to-day operations and incident response. But generating PCAP files to diagnose connectivity issues in Kubernetes clusters can be a frustrating exercise in a dynamic environment where hundreds, possibly thousands of pods are continually being created and destroyed.

Utilizing the same label-based selectors that are used for security policies, packet capture can identify single or multiple workload endpoints for capturing live traffic. In addition, role-based access control (RBAC) can be enabled with packet capture, in which case user permissions are enforced using the standard Kubernetes RBAC, based on Role and RoleBindings within a namespace.
Packet capture is an ideal solution for shift-left, self-service environments where DevOps and service owners desire greater autonomy, but require some guardrails.
DNS Dashboard: Automated DNS troubleshooting for Kubernetes
While it’s an essential part of Kubernetes, DNS is also a common source of outages and issues in Kubernetes clusters. Debugging and troubleshooting DNS issues in Kubernetes environments is not a trivial task given the limited amount of information Kubernetes provides for DNS queries.
- View the total number of DNS queries and replies
- Classify and view DNS codes by service
- Classify queries and replies by record type
- Determine the source of a query and whether it is from a workload or service
- Filter on troubleshooting scenarios
- Automatically log all DNS queries and replies
Since all query data is logged, security teams can apply Global Alerts in Calico to define alerts that are automatically triggered based on certain criteria using the logged data. Security teams can then answer the following questions:
- What DNS servers are being queried?
- How much data is being transferred and received by each pod?
- How many queries are being received?
By eliminating a lot of the manual, time-consuming introspection typically required, the dashboard accelerates troubleshooting and problem resolution in Kubernetes environments. No other vendor offers this automated capability.
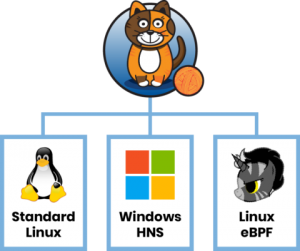
Calico Enterprise eBPF data plane: Highly performant networking, reduced resource consumption
Calico Enterprise adds support for an extended Berkeley Packet Filter (eBPF) data plane, which delivers highly performant networking, and serves as a replacement for kube-proxy to reduce resource consumption within a cluster. Calico was designed from the ground up with a fully pluggable data plane architecture, which initially supported standard Linux. As the Kubernetes footprint expands, there has been demand for a data plane that can deliver improved throughput and performance compared to the standard Linux data plane.
- Scales to higher throughput, using less CPU per GBit
- Natively supports Kubernetes services (without kube-proxy) in a way that:
- Preserves external client source IP addresses
- Supports direct server return (DSR) for reduced latency and CPU usage
- Uses less CPU than kube-proxy to keep the data plane in sync
Along with these improvements, the eBPF data plane eliminates SNAT, maintains source IP preservation using DSR, and delivers exceptional performance benefits. Calico is the only solution that offers a pluggable data plane supporting standard Linux, eBPF for modern Linux kernels, and Windows, thus future-proofing your investment in these platforms. And speaking of Windows…
Calico Enterprise: Now Available on Windows
Most enterprises have a Windows footprint, and Windows workloads are increasingly being modernized and migrated to containers and orchestrated with Kubernetes. Over the past year, we have seen an increasing demand for support for Windows nodes from enterprise users who want to deploy a single solution for Kubernetes security and observability that works across both Linux and Windows workloads. This has been driven by the need to move existing applications written in .NET/C# into a customer’s CaaS platform.

Calico Enterprise for Windows is an entirely new commercial offering that extends many of the features and capabilities of Calico Enterprise, such as policy tiers, metrics, and flow logs, to workloads that require a Windows data plane. Calico Enterprise for Windows enables all Azure customers who are interested in Windows to extend this simple yet powerful Kubernetes security and observability model to their clusters. We are also making Calico Enterprise for Windows available on other major public cloud platforms.
To read more about Calico Enterprise 3.5, see the official press release here. If video is more your style, watch this interview with TFiR where Tigera’s VP Product Management, Amit Gupta, provides details.
Ready to get started? Try a free trial.
Join our mailing list
Get updates on blog posts, workshops, certification programs, new releases, and more!