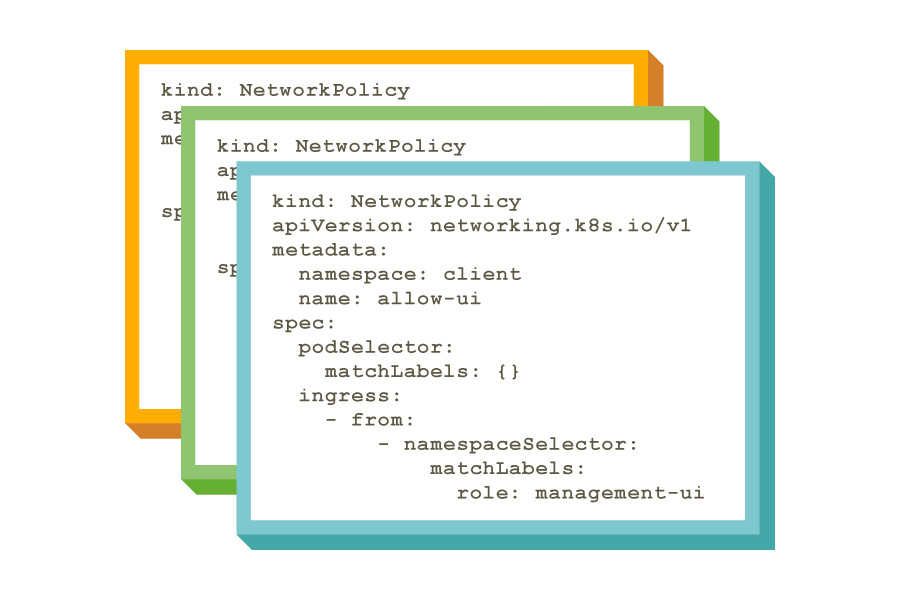
Enforce security policy as code to create immutable security artifacts for compliance.
Integrate policies into the CI/CD pipeline to ensure consistent workload access controls and microsegmentation.
Implement hierarchical policy tiers that cannot be circumvented.