Calico was designed from the ground up with a pluggable data plane architecture. The Enterprise 3.6 release introduces an exciting new eBPF (extended Berkeley Packet Filter) data plane that provides multiple benefits to users.
Great performance, lower latency for load-balanced traffic
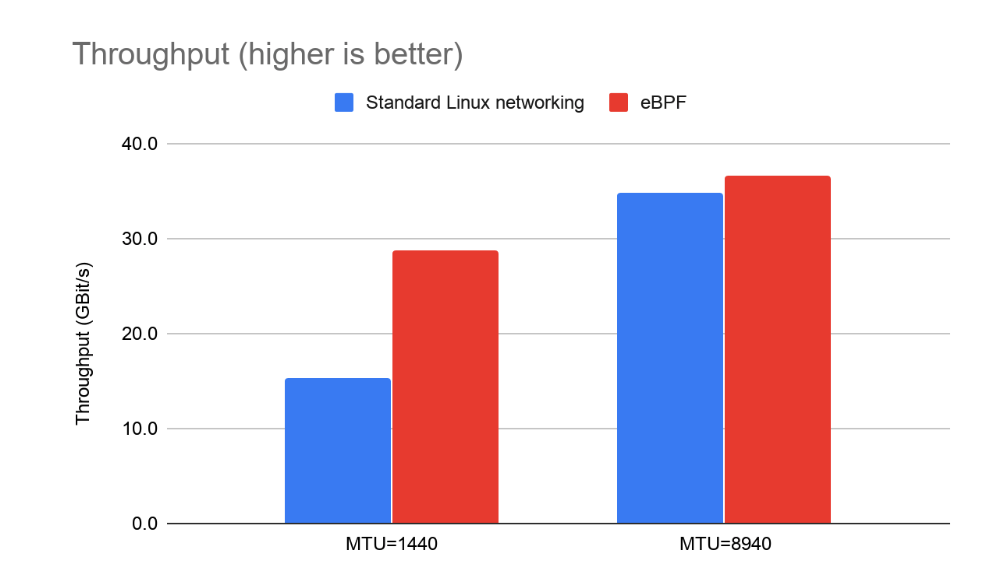
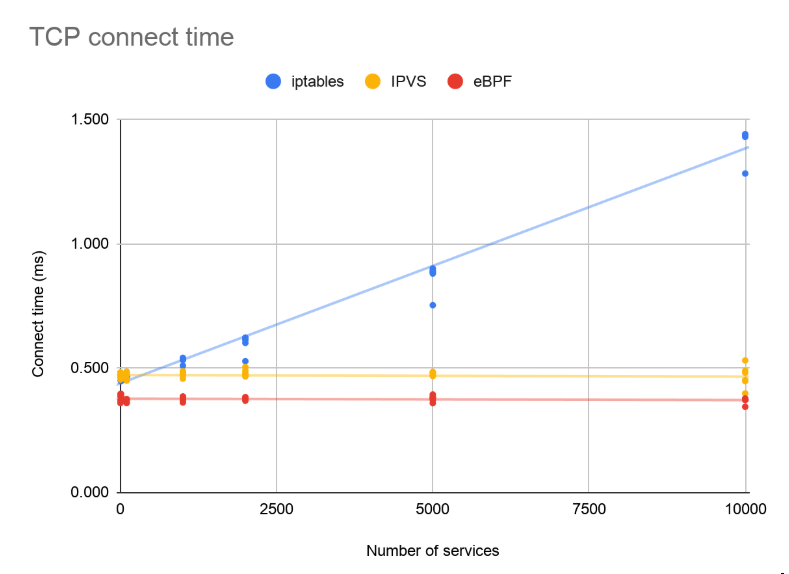
When compared with the standard Linux data plane (based on iptables), the eBPF data plane:
- Scales to higher throughput, using less CPU per GBit
- Natively supports Kubernetes services (without kube-proxy) in a way that:
- Reduces latency
- Preserves external client source IP addresses
- Supports direct server return (DSR) for reduced latency and CPU usage
- Uses less CPU than kube-proxy to keep the data plane in sync
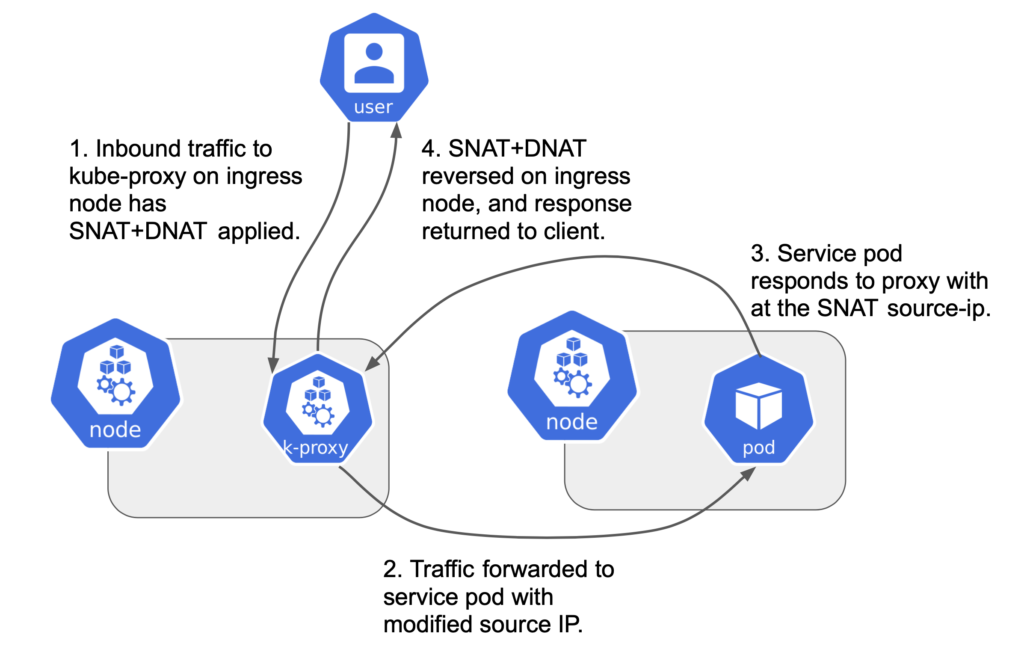
The impact of NAT on source IP
The application of network address translation (NAT) by kube-proxy to incoming network connections to Kubernetes services (e.g. via a service node port) is a frequently encountered friction point with Kubernetes networking. NAT has the unfortunate side effect of removing the original client source IP address from incoming traffic. When this occurs, Kubernetes network policies can’t restrict incoming traffic from specific external clients. By the time the traffic reaches the pod it no longer has the original client IP address. For some applications, knowing the source IP address is not only desirable, it’s required. For example, performing geo-location based on source address.
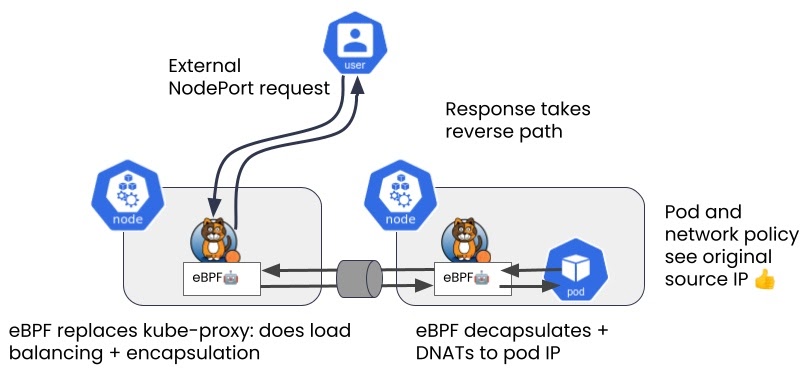
Calico and direct server return
Calico’s eBPF data plane makes several changes to this model. The most significant difference is in swapping out the Kubernetes kube-proxy with native service handling. This eliminates the need for source network address translation (SNAT). Because only destination network address translation (DNAT) is applied, the source IP address is preserved on the request. The response from the pod has a reverse DNAT applied by the eBPF program, at which point the response can be returned directly to the client, a method known as direct server return (DSR).
Support for host protection
Calico has extended its eBPF data plane to offer support for host protection. When combined with Calico’s automatic host endpoints feature, this offers a robust way to secure Kubernetes pods and hosts together using a unified policy model. By deploying Calico for host protection as well as for pod security, your host protection policy becomes just as dynamic as your workload policy, and matches the identity of the workload (carried in its metadata labels).
With this new addition, Calico now includes three data planes:
- Standard Linux
- Windows HNS
- eBPF
The standard Linux data plane will continue to be the right choice for many. But when you’re ready to adopt the latest Linux kernels, the eBPF data plane will be ready for you. And stay tuned for yet another data plane option that will soon be available for Calico.
For more details on the eBPF data plane, check out our Calico Enterprise eBPF data plane documentation. Included is a detailed comparison of eBPF versus the standard Linux data plane, as well as an architectural overview.
Want to know more? Talk to an expert to have your questions answered, or request a demo to see Calico Enterprise in action.
Join our mailing list
Get updates on blog posts, workshops, certification programs, new releases, and more!