Docker 18.09 offers the possibility for a Docker client to communicate with a remote daemon via ssh. Here’s how:
Client / Server communications
The Docker client communicates usually with the daemon either locally, via the unix socket /var/run/docker.sock, or over a network via a tcp socket. Below is a typical example of options provided to the Docker daemon at startup.
$ ps aux | grep dockerd root 2900 0.1 4.4 388008 45424 ? Sl 09:28 0:01 /usr/local/bin/dockerd -g /var/lib/docker -H unix:// -H tcp://0.0.0.0:2376 –label provider=virtualbox –tlsverify –tlscacert=/var/lib/boot2docker/ca.pem –tlscert=/var/lib/boot2docker/server.pem –tlskey=/var/lib/boot2docker/server-key.pem –storage-driver aufs
There are 2 important flags related to the client / server communication here:
- -H unix://, refers to the local unix socket /var/run/docker.sock. Locally, the Docker client uses this socket to communicate with the daemon
- -H tcp://0.0.0.0:2376 makes the daemon available via any network interface on port 2376. This port needs to be opened in the security groups (and restricted to a white list of IP addresses if possible) so a remote client can access the daemon.
As ssh is widely used and is often one of the protocols allowed by default, it could be convenient to access the Docker daemon directly via ssh. Docker 18.09 makes it possible ! Let’s test it.
Creation of a VM
We will start by creating a new Docker Host and make sure it runs the latest Docker version. We use Vagrant, a great tool from Hashicorp, to provision and configure a local virtual machine on VirtualBox. In a new folder, we run the following command :
$ vagrant init ubuntu/bionic64
This generates a file called Vagrantfile which defines how the virtual machine should be setup. We modify it a little bit so it looks like the following :
# -*- mode: ruby -*- # vi: set ft=ruby : Vagrant.configure(“2”) do |config| config.vm.box = “ubuntu/bionic64” # Bridge network configuration config.vm.network “public_network” config.vm.provision “shell”, inline: <<-SHELL # Install last version of Docker curl -fsSL http://test.docker.com -o test-docker.sh sh test-docker.sh # helper script installs the beta package # Add default user in docker group usermod -aG docker vagrant SHELL end
Basically, we tell Vagrant to :
- create a VM based on Ubuntu Bionic64
- use a bridge network so the VM is accessible from the host
- install the latest test build of Docker
- add the default vagrant user to the docker group (no more sudo on each command)
We can then create the VM with the following command :
$ vagrant up
Once the VM is up, we connect via ssh and check the network interface to get its IP address on the LAN, 192.168.5.178, in this example.
$ vagrant ssh vagrant@ubuntu-bionic:~$ ip a … 3: enp0s8: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc fq_codel state UP group default qlen 1000 link/ether 08:00:27:75:93:48 brd ff:ff:ff:ff:ff:ff inet 192.168.5.178/24 brd 192.168.5.255 scope global dynamic enp0s8 valid_lft 4242sec preferred_lft 4242sec inet6 fe80::a00:27ff:fe75:9348/64 scope link valid_lft forever preferred_lft forever
Access to the daemon over ssh
An additional folder .vagrant was created during the setup of the VM. This one contains the VM metadata and the private key which allows the default vagrant user a passwordless ssh connection. We add this key to the authentication agent with the following command (so we do not have to specify its path each time we use it) :
$ ssh-add -k .vagrant/machines/default/virtualbox/private_key Identity added: .vagrant/machines/default/virtualbox/private_key (.vagrant/machines/default/virtualbox/private_key)
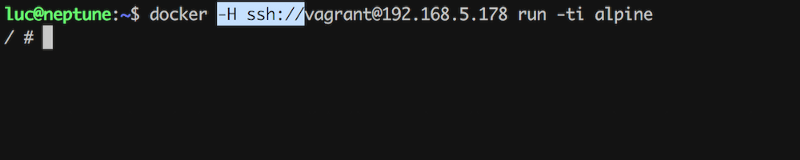
We can now issue Docker commands via ssh using the -H flag followed by the ssh connection string.
$ docker -H ssh://[email protected] run -ti alpine echo “hello” Unable to find image ‘alpine:latest’ locally latest: Pulling from library/alpine 4fe2ade4980c: Pull complete Digest: sha256:621c2f39f8133a3a94dbdf0d5ca81102b9e57c0dc184cadaf5528 Status: Downloaded newer image for alpine:latest hello
Of course, in order to avoid using this flag for each command, the DOCKER_HOST environment variable can be used instead.
$ export DOCKER_HOST=ssh://[email protected] $ docker image ls REPOSITORY TAG IMAGE ID CREATED SIZE alpine latest 196d12cf6ab1 4 weeks ago 4.41MB
Note : alpine is the only image available on the host, it was downloaded when we run the container.
This blog originated from http://medium.com/lucjuggery/docker-tips-access-the-docker-daemon-via-ssh-97cd6b44a53
————————————————-
Free Online Training
Access Live and On-Demand Kubernetes Training
Calico Enterprise – Free Trial
Network Security, Monitoring, and Troubleshooting
for Microservices Running on Kubernetes
Join our mailing list
Get updates on blog posts, workshops, certification programs, new releases, and more!