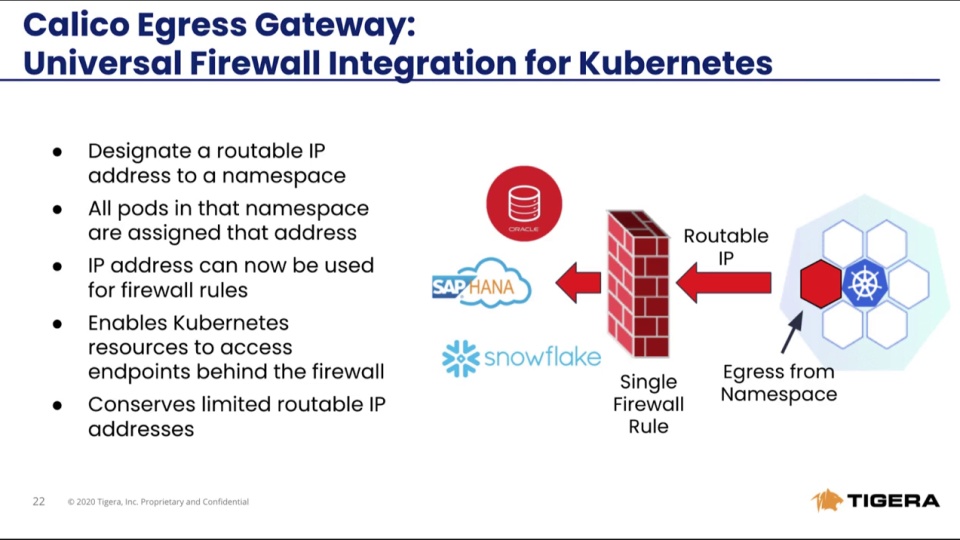
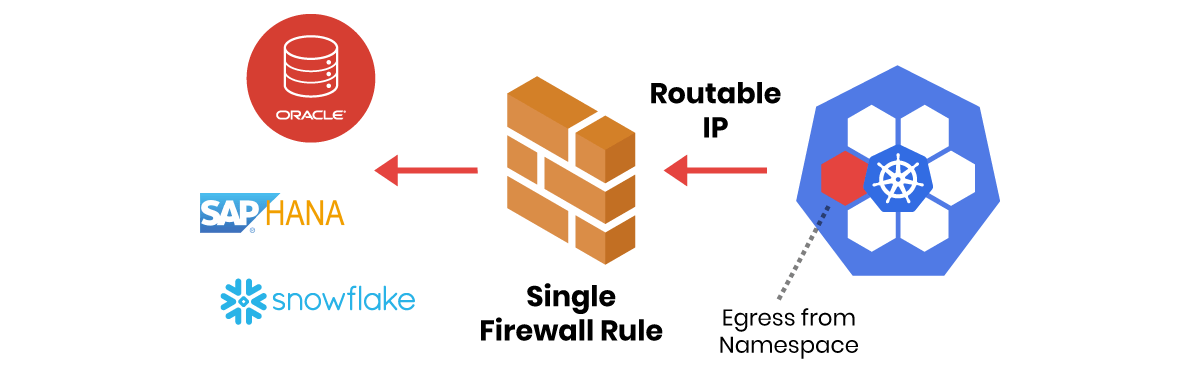
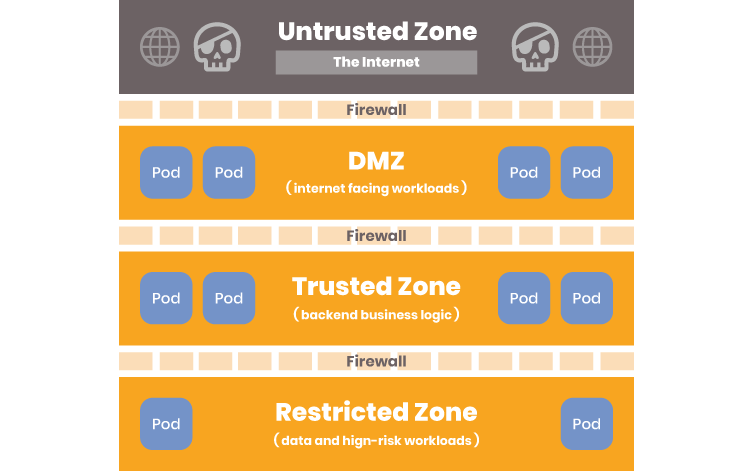
Bring your existing zone-based architecture to Kubernetes clusters and enforce the same firewall rules by translating them into Kubernetes security policies using Calico.
Explicitly allow-list which microservices are permitted to traverse zones and achieve compliance.