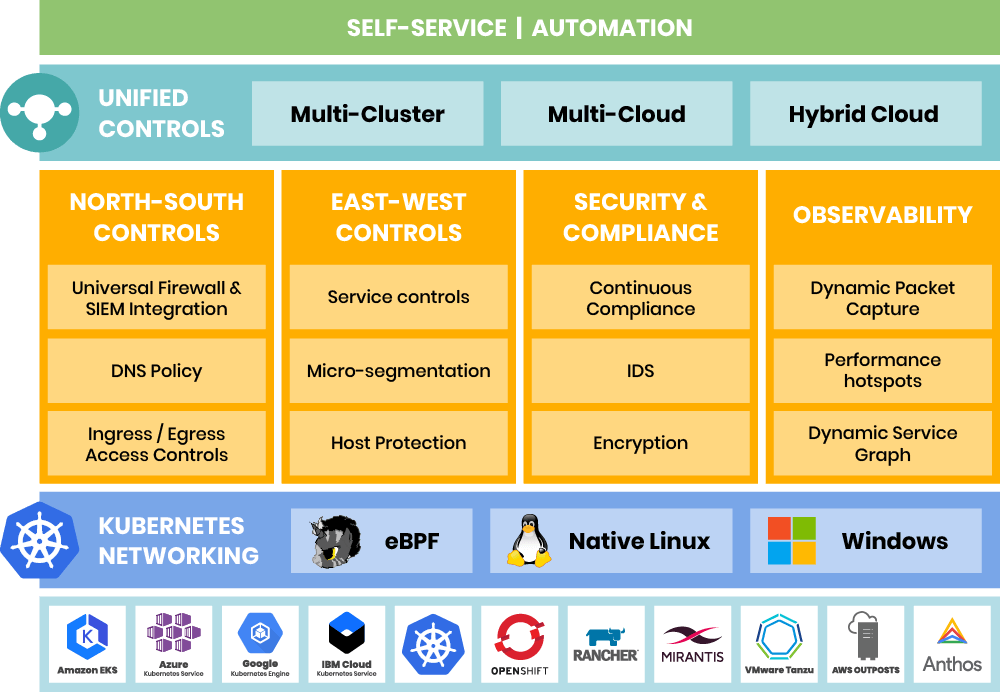
As we enter a new year, it’s an appropriate time to reflect on our achievements at Tigera and how much Calico Enterprise has evolved over the past year as the industry’s leading Security and Observability solution for Kubernetes Networking and Microservices. Our experience working with enterprise-class early adopters has helped us to identify the most critical requirements for them to operationalize their Kubernetes deployments and successfully make the challenging transition from pilot to production. These learnings have helped us to shape today’s Calico Enterprise, which is visually represented in this solutions architecture diagram. Let’s dig into this feature-rich layer cake of functionality, from bottom to top!
Calico Enterprise Solutions Architecture
Calico Enterprise is “Kube-native”
But first, there are some important things to keep in mind as we explore. Calico Enterprise is a Kubernetes-native solution – Kube-native – in which everything we do is an extension of Kubernetes primitives. We leverage the full power of Kubernetes by integrating with the Kubernetes API server and creating our own aggregated API server. We use an operator model to access and control custom resources to perform specific functions, like RBAC for example, natively in Kubernetes. Being Kubernetes-native means that as Kubernetes evolves, Calico Enterprise will automatically maintain compatibility and remain future-proof.
A Common Security Model that Works Anywhere
As a critical foundational element, Calico Enterprise provides a common security model that works across heterogeneous environments. Operationally, that means it will work with any public cloud service in a hybrid or multi-cloud configuration, and with any Kubernetes distribution, and with VMs and bare metals. In addition, most of the largest public cloud providers and Kubernetes distributions have chosen our solution and have worked with us to tightly integrate with it.
Why is this important? Many of our customers have a multi-cloud and hybrid cloud strategy (one of them uses four cloud services) and have adopted Kubernetes because it is an abstraction that can run on any cloud infrastructure. And because Calico Enterprise can run any cloud, and on any distro, it is the logical choice for cloud architects and platform teams who want a solution that will easily adapt as their requirements change over time. Many of our customers also have a mix of Kubernetes and non-Kubernetes workloads and chose Calico Enterprise because they needed a single solution that works across both of these environments.
Pluggable, Future-Proof Data Plane – Standard Linux, Windows and eBPF
Calico Enterprise was designed from the start with a fully pluggable data plane, so customers can choose the right data plane for the right job. The Kubernetes networking layer highlights the three data planes that we offer. Most of our customers use the standard Linux kernel data plane because they aren’t yet running the latest versions of Linux required to support eBPF. A small number of application workloads are running on Windows and for those customers we provide a single solution that works across Linux and Windows. For users who want to push the performance limits using the latest Linux kernels, we also offer an eBPF dataplane. Inevitably, a faster dataplane technology will emerge in the next few years and we plan to add support for it. This is another way Tigera is future-proofing our customers’ investment in Calico Enterprise and showing our commitment to providing the most advanced, scalable, and reliable solutions for Kubernetes users.
Now, let’s look at the four pillars across the center of the diagram that highlight our Security and Observability capabilities.
North-South Controls
Calico Enterprise provides both north-south and east-west security controls. However, it is in the north-south interface between the Kubernetes cluster and the external IT environment that we encounter the highest levels of concern about security. Using our DNS policy controls and ingress/egress access controls our customers can securely control north-south traffic. The Calico enterprise universal firewall and SIEM integration are two methods that support the integration of existing enterprise security controls with the Kubernetes environment.
East-West Controls
East-West controls enable you to limit the blast radius when a security breach results in an APT (advanced persistent threat), and there are several ways that we help you to establish these controls. The Calico Enterprise “defense-in-depth” approach provides protection on three levels: host, container/VM and application. Using a single policy framework, you can set controls at all of these levels using a declarative model. You can also set very fine-grained access controls and filter traffic at the application protocol level, for example by http, https or MongoDB protocols. We also enable you to perform micro-segmentation for both container and VM workloads.
Security and Continuous Compliance
As the Kubernetes footprint expands, we’ve seen demand for an even greater in-depth approach to protecting sensitive data that falls under regulatory compliance mandates. For security and continuous compliance, Calico Enterprise provides data-in-transit encryption with industry leading performance, as well as continuous compliance reporting for security policies and controls. We also have an incredibly rich Intrusion Detection feature set that includes threat feeds that identify known bad actors like bots, custom alerts for known attacks, anomaly detection, and honeypods. We take an automated approach to malware detection and response. For example, we created a machine learning algorithm in Calico Enterprise which specifically targets the DGA (Domain Generation Algorithm) use case and identifies anomalous behavior, making it easy for security teams to detect DGA activity. Calico Enterprise can also trigger automated remediation by removing a rogue microservice from the network in milliseconds and then generating policy recommendations to prevent a future attack.
Observability and Troubleshooting
Downtime is expensive and distributed applications are very difficult to troubleshoot. Calico Enterprise can dynamically generate a Service Graph that enables anyone to easily understand how microservices are behaving and interacting with each other at run-time, simplifying the debugging process. The Dynamic Service Graph provides a very rich set of information including, across which namespaces workloads are communicating, detailed DNS information, detailed flow logs for every single flow in your cluster, and how network policies are being evaluated. Performance hotspots are automatically identified and highlighted, and alerts are provided in the context of the service graph. With this solution in place, software engineers can quickly identify the source of a problem at the application, process, and socket levels as well as through an automated packet capture function.
Unified Controls and Self-service / Automation
Unified controls enable security and observability across multi-cluster, multi-cloud and hybrid cloud environments, and provide a single pane of glass to ensure consistent application of security controls. They also support self-service security and CI/CD integration for advanced users. Calico Enterprise has operationalized the concept of policy tiers, which support delegation of authority by organizational structure and area of responsibility for the various teams that have different needs (security, networking, platform, devops, SRE, dev). Policy tiers define the order in which network security policies are evaluated, and are used to implement security controls that cannot be changed or overridden by unauthorized users. Enterprise-wide access controls created by the security team, for example, have primacy and are on the highest tier. Policy tiers can federate across multiple clusters using the centralized control capabilities of Calico Enterprise, enabling a single definition of security controls that can be applied to all clusters.
Join our mailing list
Get updates on blog posts, workshops, certification programs, new releases, and more!