We are excited to announce the early preview of Calico Enterprise 3.16. This latest release extends the active security platform’s support for egress access controls, improves the usability of network-based threat defense features, and scales visualization of Kubernetes workloads to 100s of namespaces. Let’s go through some of the highlights of this release.
Egress gateways for Microsoft Azure and AKS
Egress gateways allow you to identify the source of traffic at the namespace or pod level when it leaves a Kubernetes cluster to communicate to external resources. This makes it highly beneficial for security teams to apply access controls to specific traffic instead of opening up a larger set of IP addresses. Calico Enterprise 3.16 has added egress gateway support for Microsoft Azure and AKS in addition to our support for AWS and EKS. Check out our documentation, Configure egress gateways, Azure, to learn more.
Operator-managed deployments of egress gateways
Calico Enterprise now includes operator-managed deployments of egress gateways. This reduces operational overhead and eliminates additional steps required during software upgrades. With the Tigera Operator, egress gateways will always be automatically upgraded.
UI for workload-based web application firewalls (WAF)
Calico Enterprise’s unique workload-centric web application firewall (WAF) offers runtime threat detection for application-layer traffic in your Kubernetes cluster. It builds on Calico’s Envoy-as-DaemonSet architecture to provide an operationally simpler alternative to a service mesh, enabling visibility into application-layer (layer 7) traffic and the detection of potential indicators of compromise. Calico Enterprise 3.16 features a new Manager UI that can be used to enable and configure a workload-based WAF. This update will simplify your WAF deployments and allow you to manage alerts right from the Manager UI.
Service Graph performance optimizations
Our Dynamic Service and Threat Graph has become the focal point of many Calico Enterprise deployments, as it provides a way to visualize the communication between applications and services, initiate and retrieve packet captures, troubleshoot issues, and much more. This release of Calico Enterprise includes several optimizations to improve the performance of the Service Graph for clusters with larger numbers of namespaces.
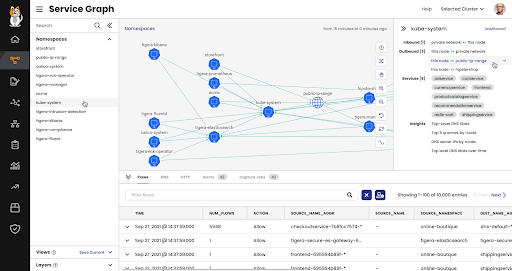
Fig 1: Dynamic Service and Threat Graph with Calico Enterprise
Support for multiple external networks
Some of the largest telecommunications providers in the world use Calico to run their 5G networks on Kubernetes. Calico Enterprise now includes networking options that allow pods from different namespaces to egress onto different external networks (virtual routing functions or VRFs) that may have overlapping IPs with each other. This also enables administrators to configure which service IPs are advertised for a network by the service IP advertisement feature.
Improved product security with more restrictive SecurityContext
Calico Enterprise has updated its components to apply a more restrictive SecurityContext where applicable. This includes:
- Non-root context whenever possible and added drop
ALL Capabilities - Root context and privilege escalation are used only when necessary
- SeccompProfile is set to RuntimeDefault
Conclusion
We hope you’ll enjoy these product upgrades and enhancements. We will continue to deliver new releases with innovative solutions to solve container and Kubernetes security challenges. Watch this space for future updates.
Check out our self-paced workshops for an in-depth product experience.
Join our mailing list
Get updates on blog posts, workshops, certification programs, new releases, and more!


