Assess your Kubernetes environment’s control plane components to harden configurations.
Customize compliance reports and prioritize issues when assessing workloads against hardening standards such as CIS benchmarks.
Continuous monitoring and reporting of misconfigurations in Kubernetes environments based on CIS benchmarks.
Real-time view of traffic flows within and outside Kubernetes clusters to understand service dependencies, view policy enforcement, and more
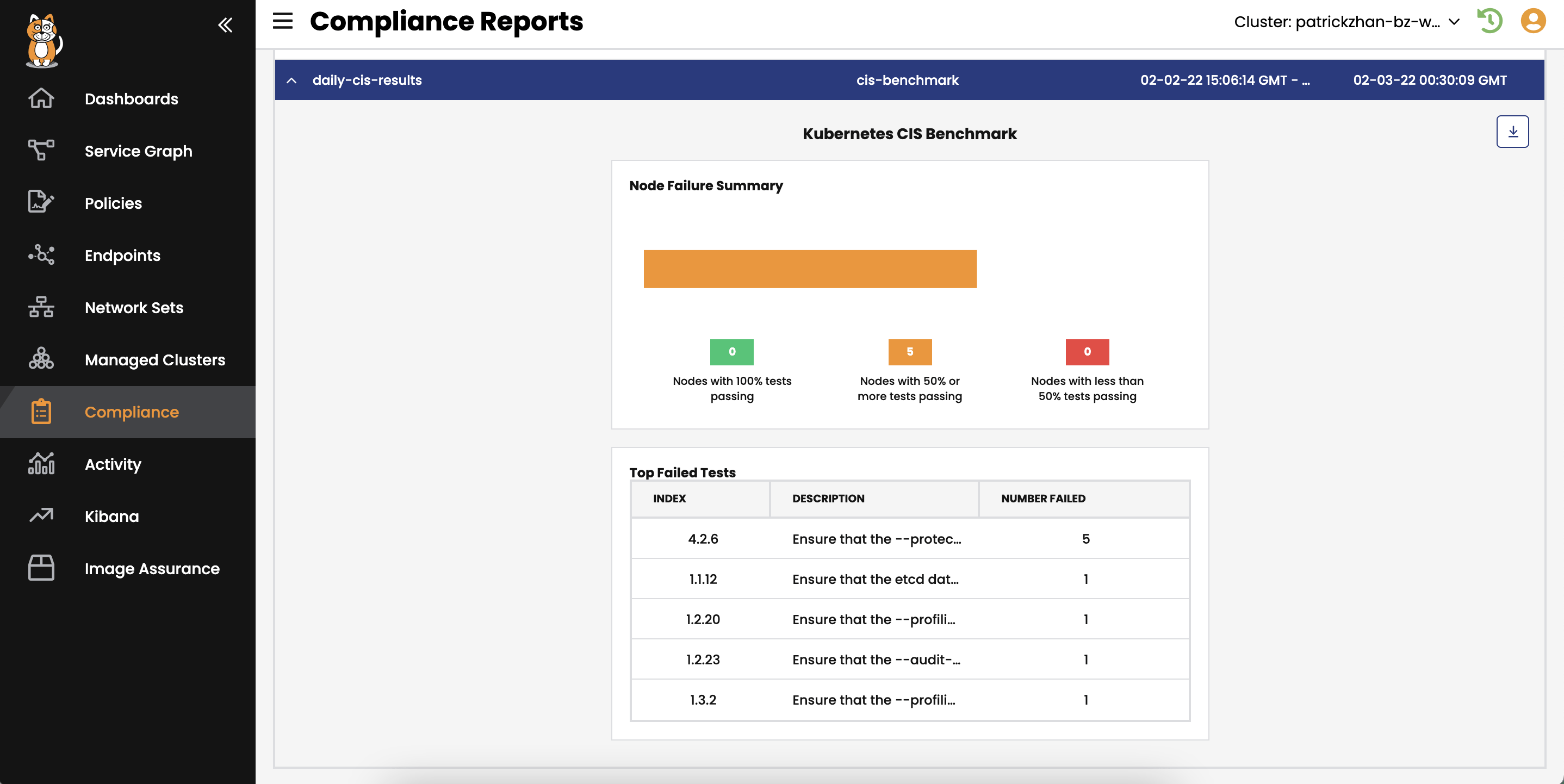
Assess your Kubernetes environment’s control plane components to harden configurations.
Customize compliance reports and prioritize issues when assessing workloads against hardening standards such as CIS benchmarks.
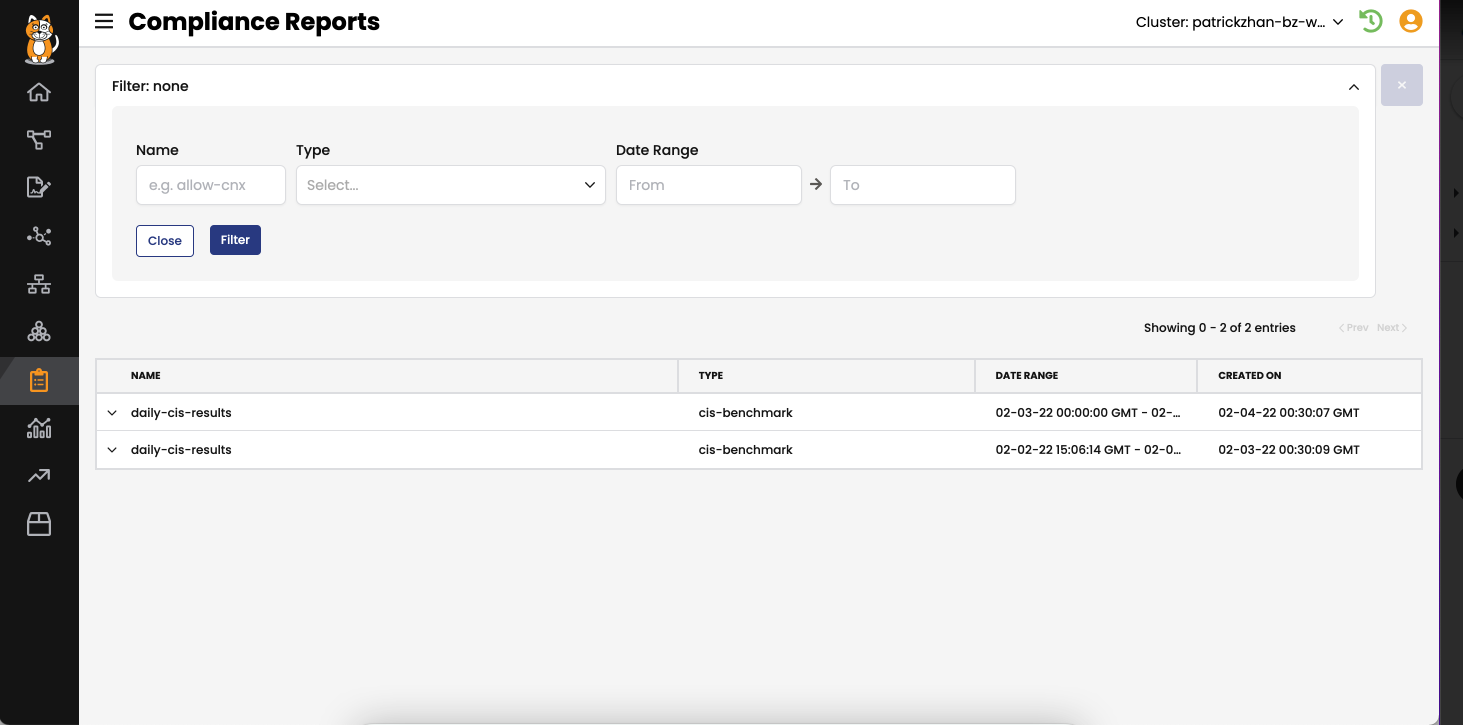
Manage configuration security by generating CIS benchmark reports across all the dynamic assets that may have existed in your Kubernetes environment.
Gain valuable insight into workload security posture with customizable pass/fail thresholds.
Get started right away on Azure or AWS—every Calico component you need to get up and running is ready to go.
Here’s what our customers are saying about us
It’s extremely helpful to know what endpoints your services are talking to. With Calico Cloud in place, we have a much-improved security posture.
Developer-created resources to help you secure your Kubernetes deployment


Start a free trial or contact us to see Calico in action