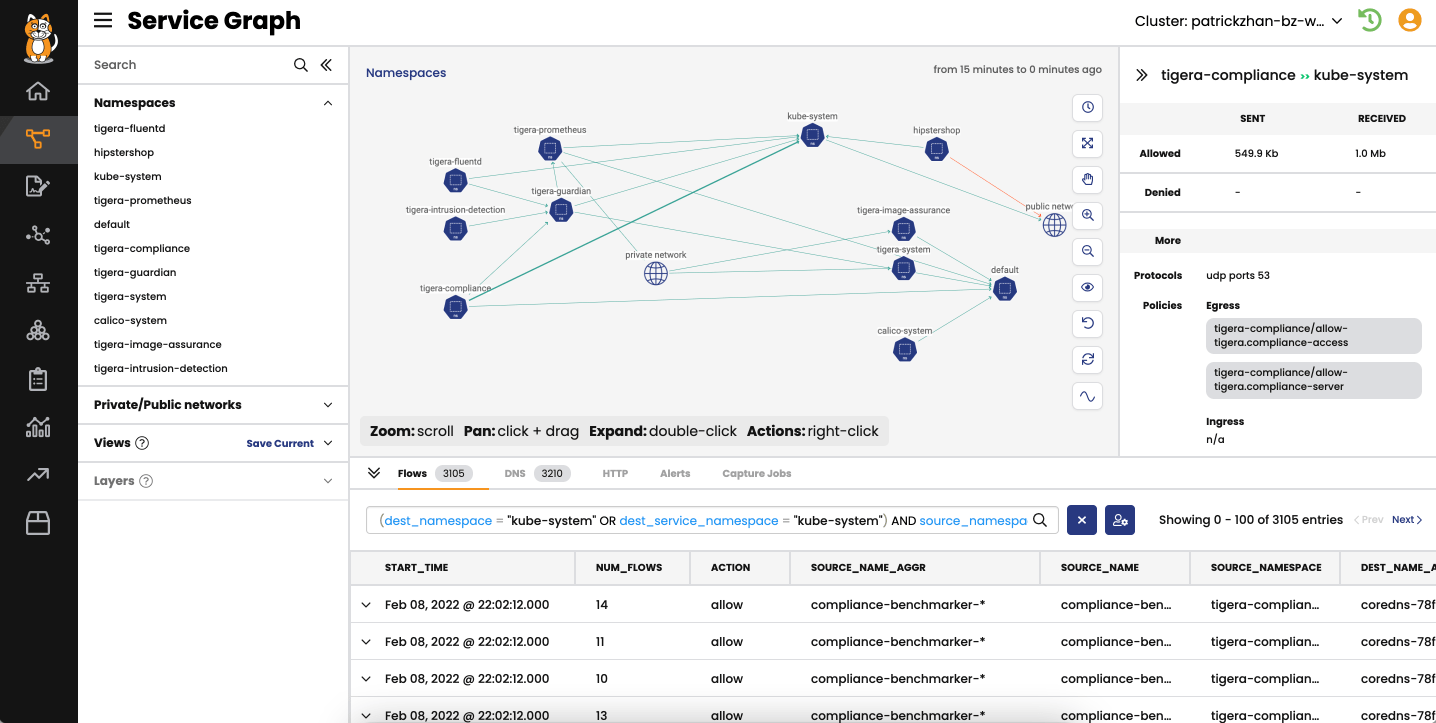
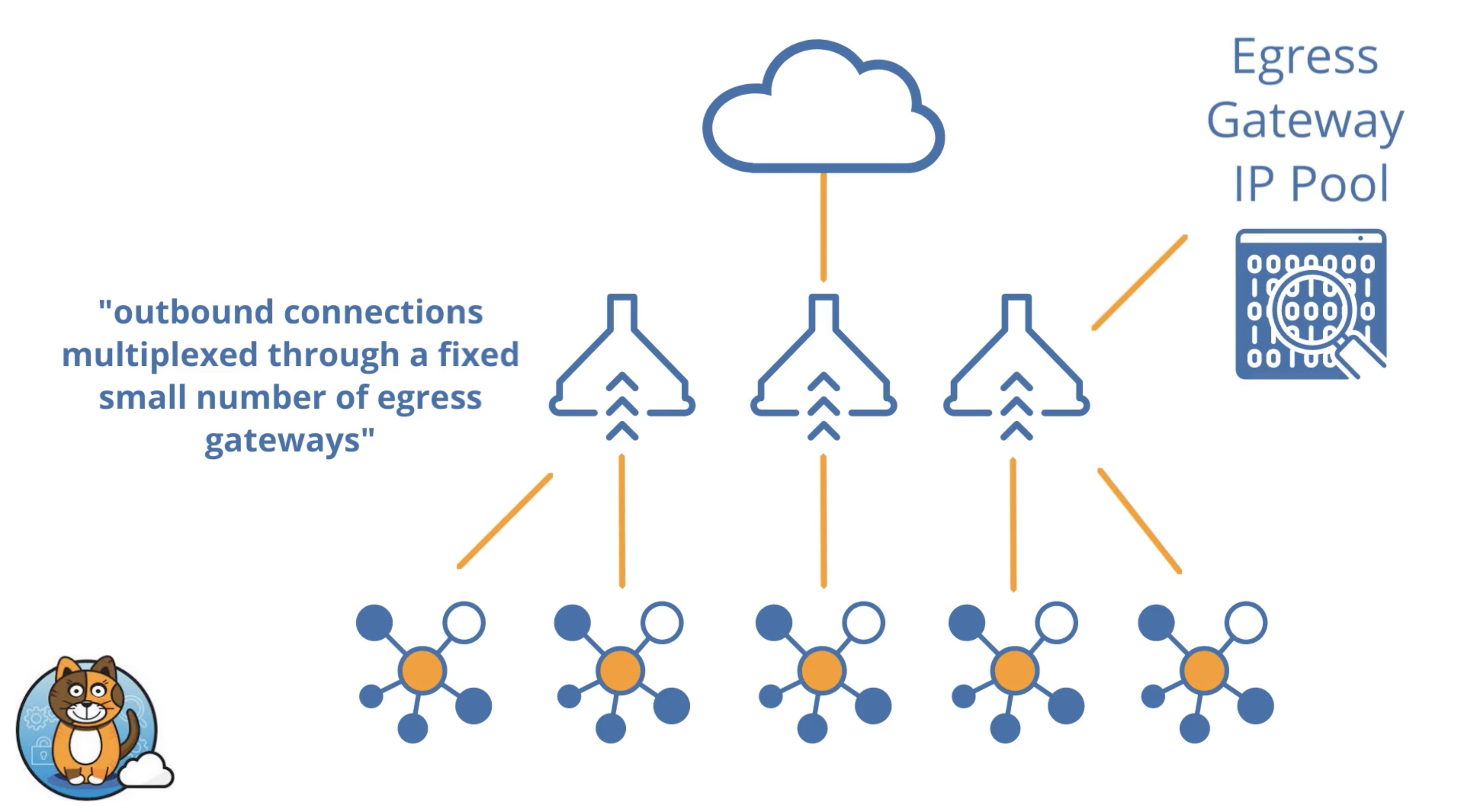
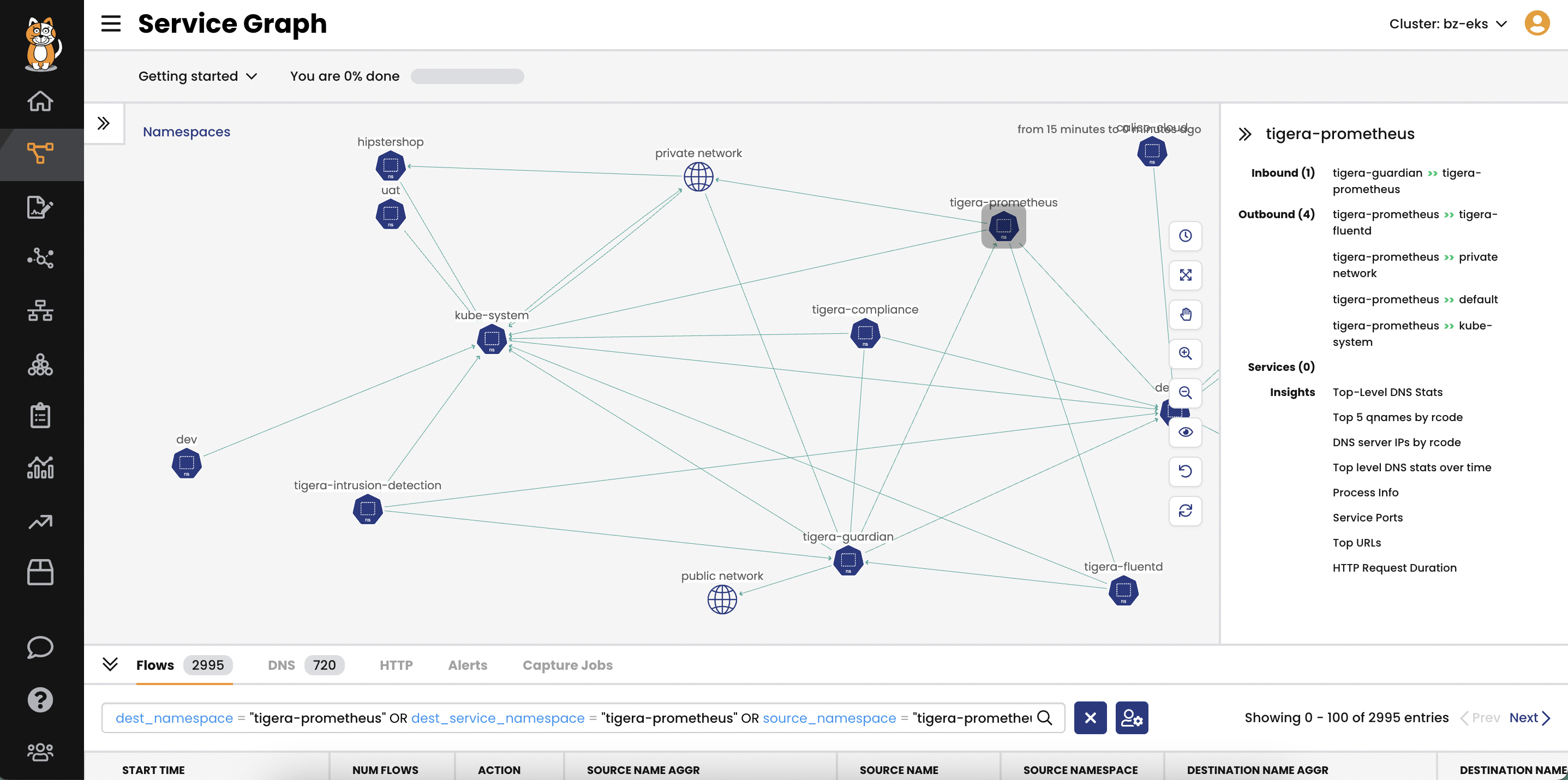
Secure access from individual pods in Kubernetes clusters to external resources, including databases, internal applications, 3rd-party cloud APIs, and SaaS applications.
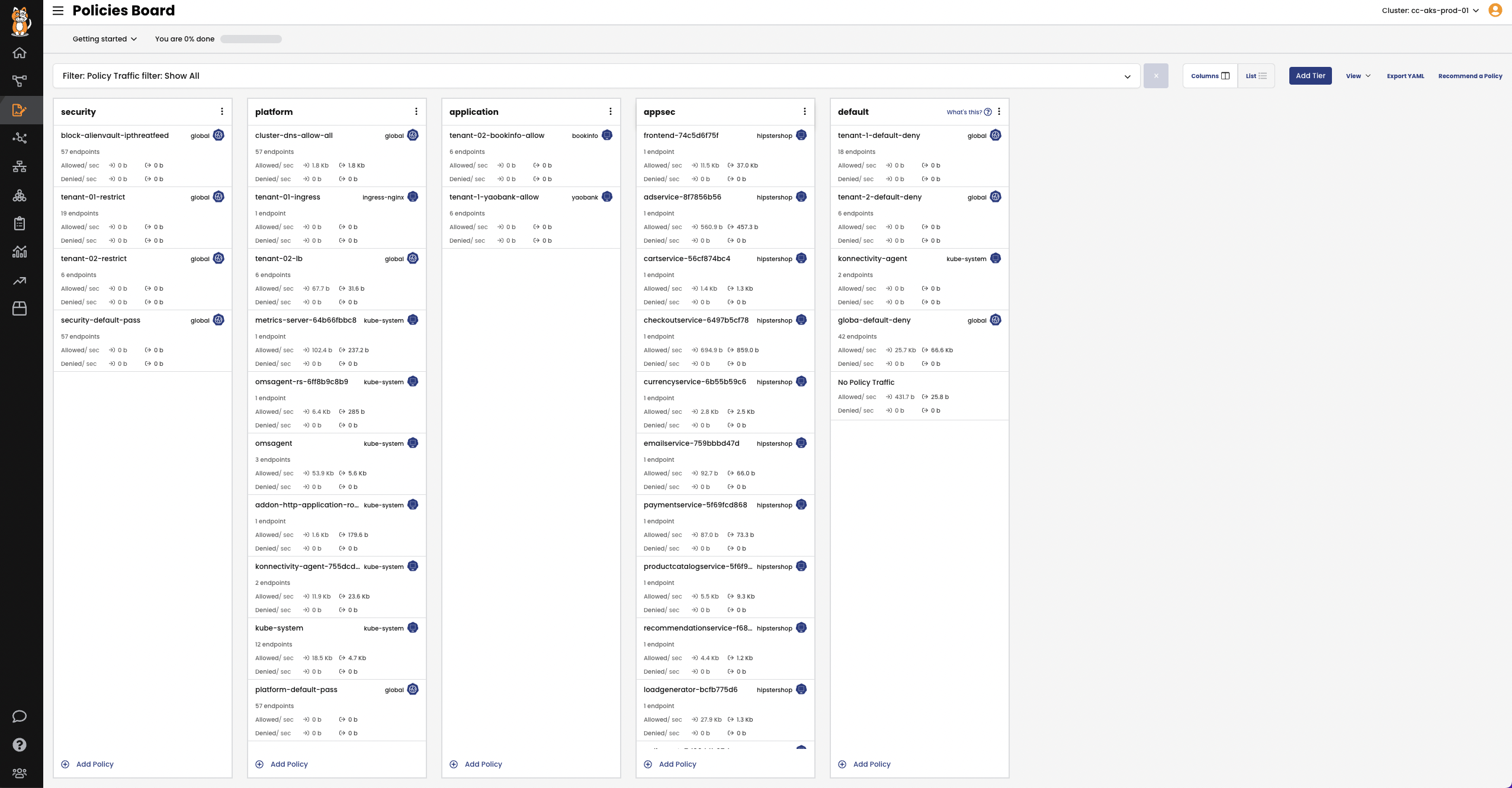
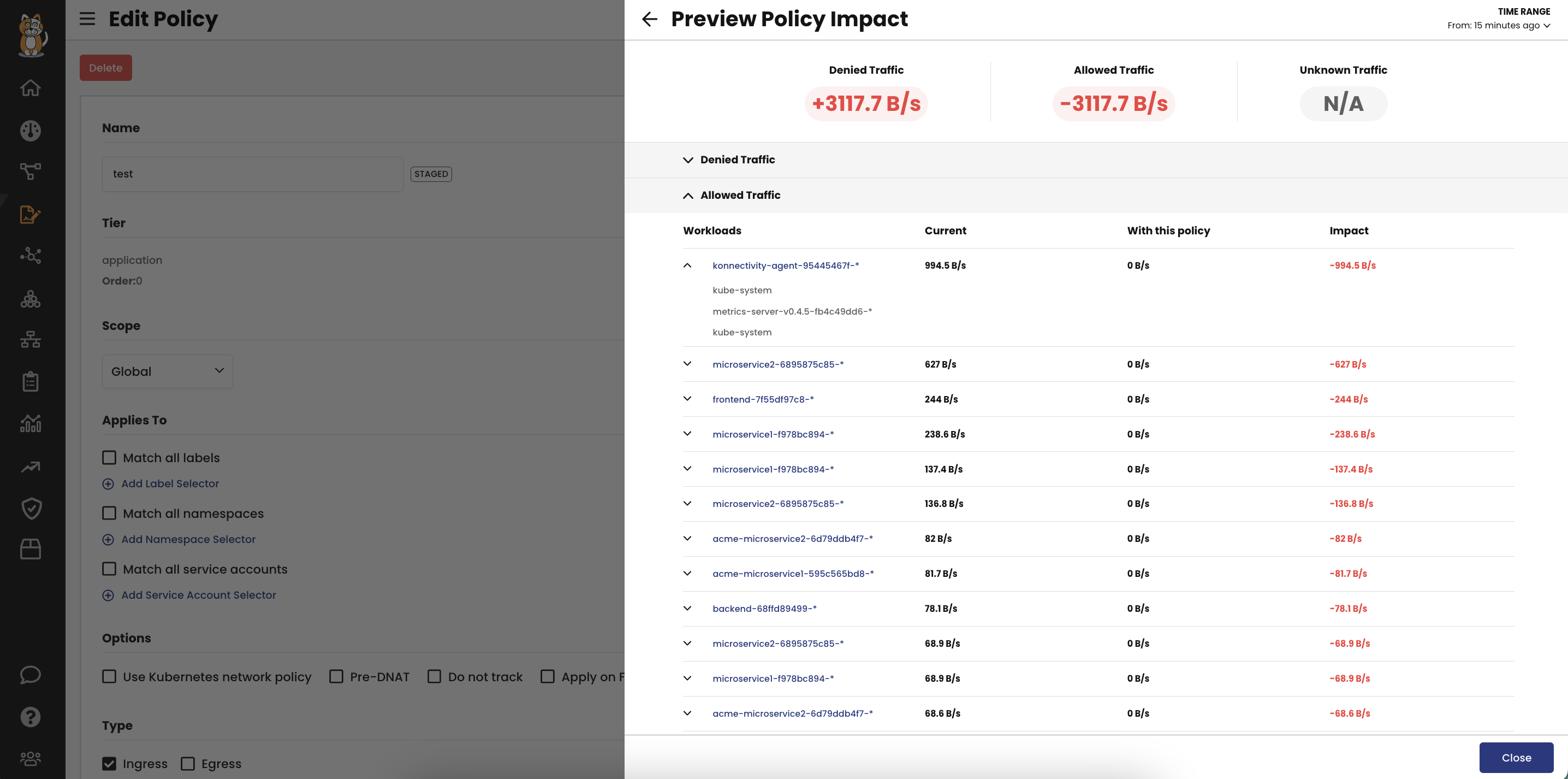
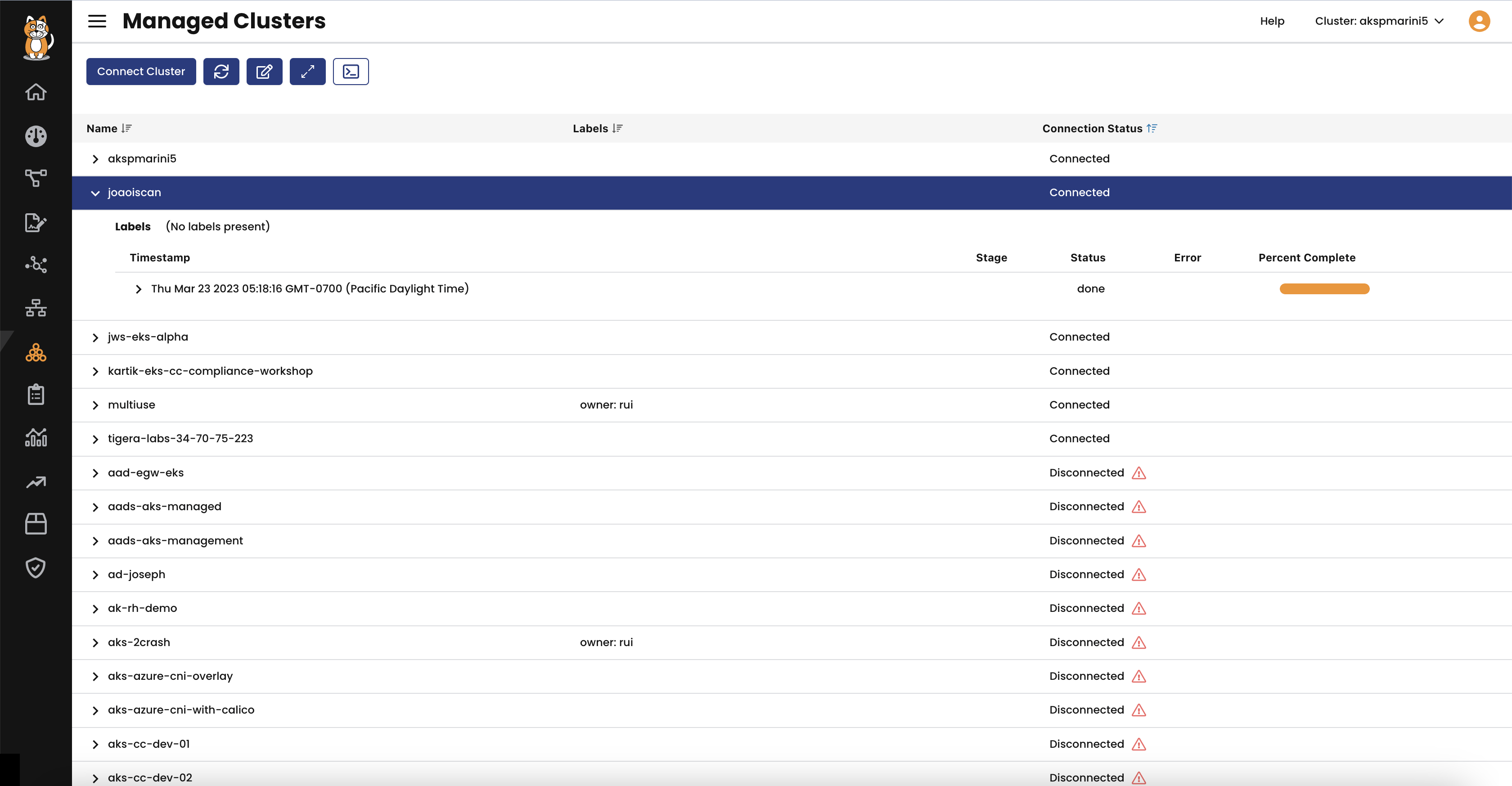
Deploy granular workload access controls using DNS egress policies to enforce controls and NetworkSets for access control using IPs/CIDRs.