SUSE Rancher
Rancher with Calico provides active, zero-trust based security for cloud-native applications running on containers and Kubernetes

Overview
Rancher builds innovative, open-source software that makes it easy to deploy and manage containers in production on any infrastructure. Rancher natively integrates with Calico Cloud for active, zero-trust based security for cloud-native applications running on containers and Kubernetes. SUSE has added open source Calico container network interface (CNI) plugin as an option to Rancher Kubernetes Engine (RKE) 2, enabling consistent Kubernetes network policy definition and enforcement. Additionally Calico Enterprise is now available on RKE2 providing zero-trust workload access with observability and troubleshooting capabilities.
Benefits
With a shared vision of helping our customers capitalize on the benefits of modern applications orchestrated by Kubernetes, Rancher and Tigera partner to provide our customers with innovative open-source software solutions.
- Rancher is now part of SUSE. Scale with SUSE Rancher and get access to world class commercial support alongside the same great platform experience.
- Rancher customers who require enterprise security capabilities, have compliance requirements, and need to integrate their Rancher clusters with their existing IT infrastructure will benefit from Calico’s enterprise features including:
- Support for hybrid and multi-cloud environments
- Ability to define, declare, and enforce a consistent, unified network policy and security model across all Kubernetes clusters, whether managed or self-hosted
- The Rancher and Tigera integration enables you to leverage Rancher’s centralized management functionality with Calico’s unified controls for security and observability, to protect and manage all your Kubernetes clusters wherever they run.
- Tigera and Rancher work together to provide active, zero-trust based security for cloud-native applications running on containers in Rancher RKE and RKE2.
- Robust build-time security with safeguards for Rancher RKE and RKE2 applications.
- Create and enforce compliance via security policies in RKE and RKE2 as per regulatory and organizational requirements.
- Identify and resolve connectivity issues and security policy violations between namespaces, microservices, and pods in Rancher clusters.
Top Use Cases
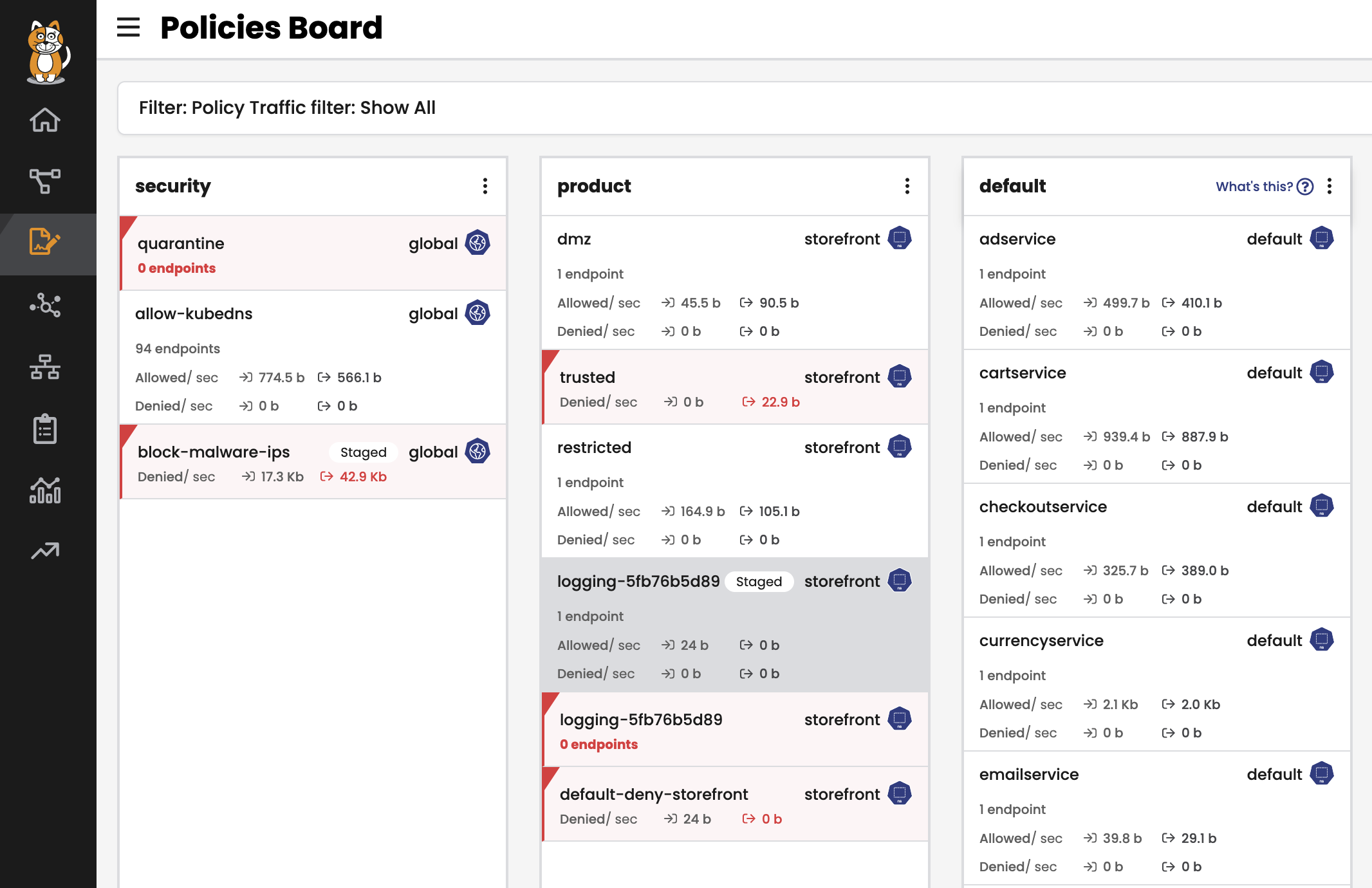
Zero-trust Workload Security
Security teams need to control the flow of data between Kubernetes clusters and external resources, in order to mitigate the risk of unauthorized access to applications and data, exposure of sensitive data such as personally identifiable information (PII), and introduction of malware and ransomware.
Implement zero-trust workload access controls and protect containerized environments in Rancher RKE and RKE2 from outside threats, while enabling applications and workloads to securely communicate with resources outside the cluster behind a firewall or other control point.
KEY FEATURES INCLUDE
- Zero-trust workload access controls
- Identity-aware microsegmentation
- Universal Firewall Integration
- Envoy-based application-level protection
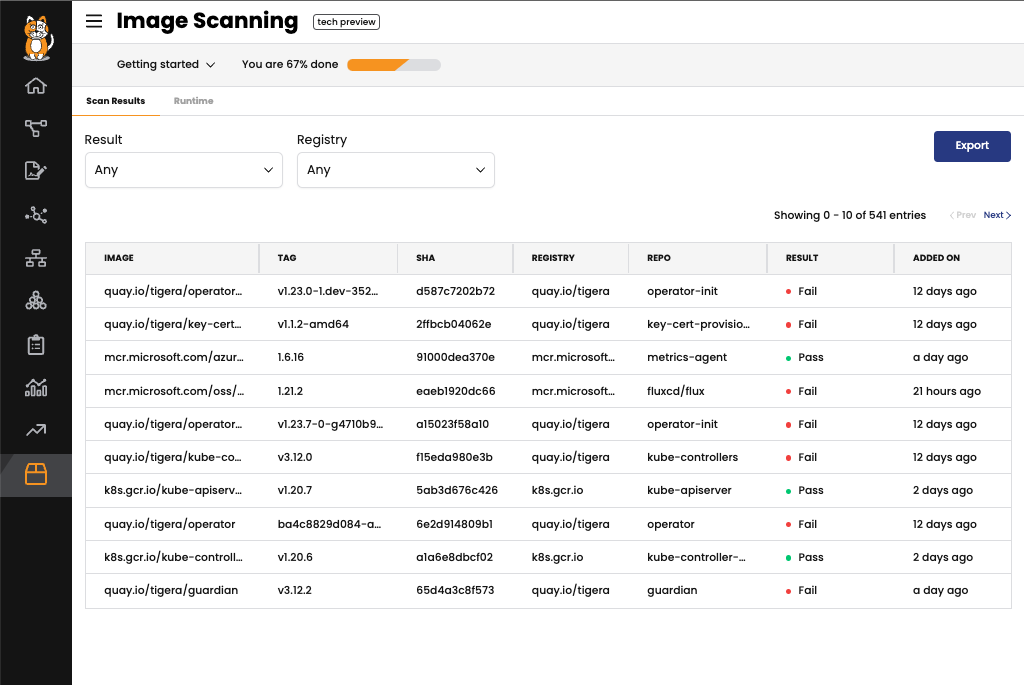
Container Security
Container images may contain vulnerabilities. To ensure developers are not introducing critical issues into the production environment, DevOps and Security teams should scan and block images for both vulnerabilities and configuration issues.
Protect containers during development and production. Reduce attack surface with vulnerability and misconfiguration detection. Provide runtime protection from known threats and zero-day vulnerabilities.
KEY FEATURES INCLUDE
- Image assurance
- Configuration assessment
- Runtime Threat Defense
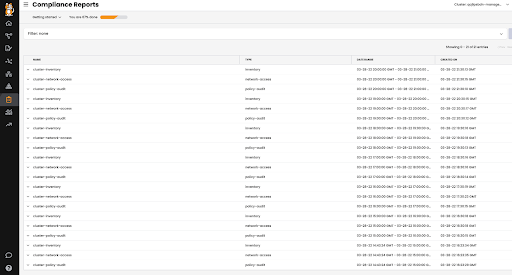
Regulatory and Compliance
Businesses, subject to corporate and/or regulatory compliance requirements, need to isolate workloads containing sensitive data or restrict access to specific resources. Auditors need proof of control enforcement, but capturing the information required to show proof is challenging, especially in a dynamic, distributed microservices environment where containers are short lived.
Create compliance reports for any compliance framework including PCI, SOC 2, and more. Continuously monitor compliance for your container, Kubernetes, and cloud environments. Retain a daily history of your compliance status. Generate on-demand or scheduled audit reports.
KEY FEATURES INCLUDE
- Encryption
- Security Controls
- Evidence and audit reports
- Configuration security
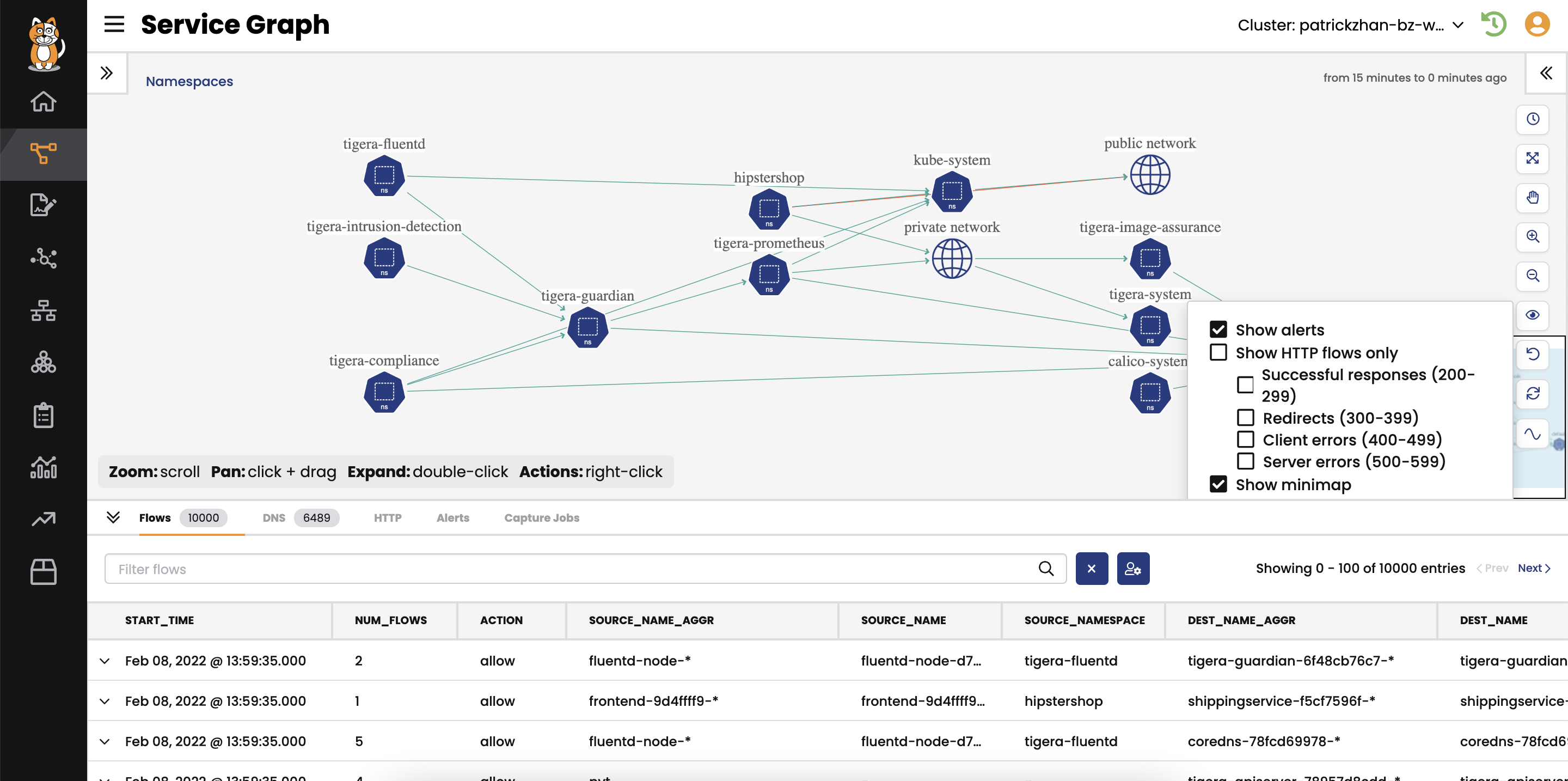
Observability and Troubleshooting
Kubernetes workloads are highly dynamic, ephemeral, and are deployed on a distributed and agile infrastructure. As a result, fast troubleshooting of Kubernetes workloads is challenging. Teams require better visibility, and contextual information for microservices, their dependencies, how they are interconnected, and which other clients and applications access them.
Enable faster troubleshooting of workloads and cloud-native applications with Dynamic Service and Threat Graph, Dynamic Packet Capture, anomaly detection, and performance hotspots, leading to shorter time-to-resolution, less application downtime, and improved quality of service.
KEY FEATURES INCLUDE
- Dynamic Service and Threat Graph
- Dynamic Packet Capture
- Performance Hotspots
How It Works
Connect your RKE cluster to Calico Cloud
Calico enables cloud users in Rancher RKE and RKE2 to avail of active, zero-trust based security for cloud-native applications running on containerized workloads and in Kubernetes. Its Cloud-Native Application Protection Platform (CNAPP) prevents, detects, troubleshoots, and automatically mitigates exposure risks of security issues in build, deploy, and runtime stages.
Install Calico Enterprise on RKE clusters
Alternatively, Calico Enterprise offers the same feature-rich security & observability as a self-managed solution for organization’s with complex networking design choices or for clusters running in air-gapped environments.
Key Capabilities
Get Started
Getting started with Calico and Rancher RKE is easy and free.
Everything you need to get Calico installed and configured in your Rancher RKE cluster is available here:
Resources
Blog
Simplified Networking, Security and Observability for Rancher Kubernetes Engine with Calico
Learn More