As innovations in the world of application development and data computation grow every year, the “attack surface” of these technologies grows as well. The attack surface has to be understood from two sides—from the attacker’s side and from the organization being attacked. For the attacker, they benefit from the entry point into a system, either through the ever-growing perimeter of public-facing applications or the people managing these applications, because the probability of finding a weakness to enter from these entry points is higher. For the organization, managing the attack surface requires investing in more security tools and personnel. This can cascade into bigger security issues, which is why addressing the attack surface is essential.
The MITRE adversarial tactics, techniques, and common knowledge (ATT&CK) framework can help us understand how this large attack surface can be exploited by an adversary and how they strategize an attack. In this two-part blog, I will cover the new ATT&CK matrix for containers and how Calico provides mitigation solutions for each tactic in the matrix. In this blog, we will explore the first four tactics, which mostly deal with reconnaissance. In the second part, we will discuss the techniques and mitigation strategies once an attacker has gained access.
MITRE ATT&CK framework and matrix
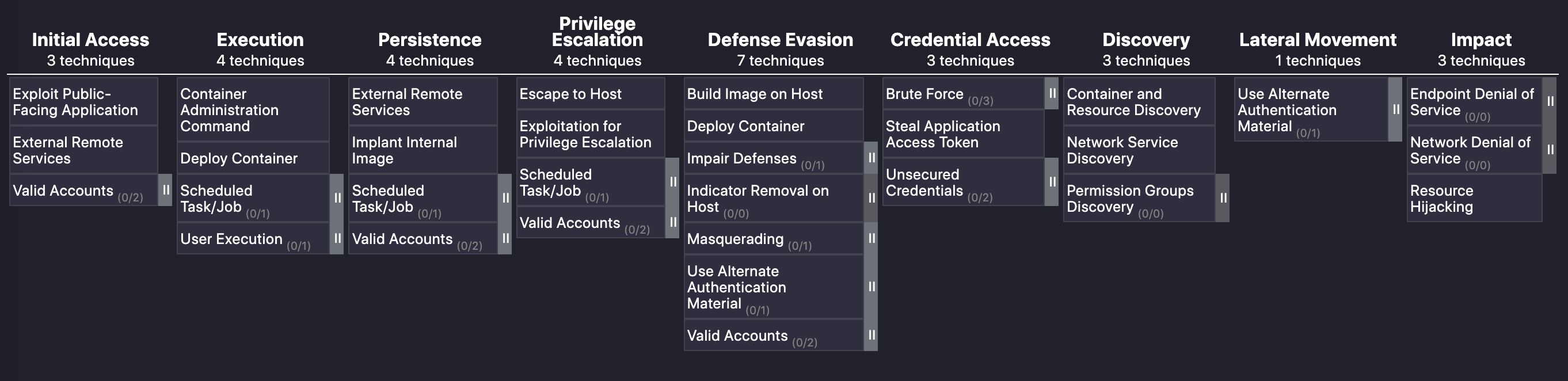
The MITRE corporation came up with ATT&CK, a cybersecurity framework that uses a typical cyber kill chain to explain tactics, techniques and mitigation strategies for enterprises. MITRE recently added a matrix (tactics and techniques in a tabular form) for containers after considering new techniques unique to container technology. As with other platforms, the matrix for containers starts with initial access, or how attackers can enter an organization’s environment to cause monetary or data loss.
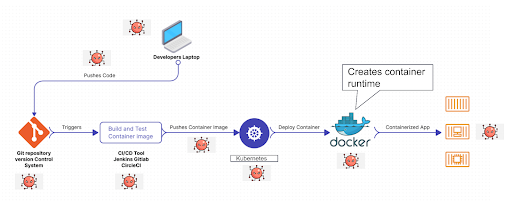
Let’s further explore these concepts with an example. Consider a sample application built with microservices. The flow diagram below shows multiple areas within a container-based application that an attacker will try to exploit. This attack area ranges from build time—when a developer is writing code, checking-in the code to a repository—to runtime, when a developer is building container images from base images and running the containers in Kubernetes clusters.
How does the MITRE ATT&CK framework relate to the figure above? The matrix for containers shown below (fig. 2) is a table with multiple columns for tactics and below each tactic is the technique.
From MITRE:
Technique – Techniques represent how an adversary achieves a tactical goal by performing an action. For example, an adversary may dump credentials to achieve credential access.
Tactic – Tactics represent the “why” of an ATT&CK technique or sub-technique. It is the adversary’s tactical goal: the reason for performing an action. For example, an adversary may want to achieve credential access.
The framework shows that each stage can be thought of as a gate to stop the attack from happening. The lock is in your hand, and how difficult you make it for the attacker to get the key is where the defense-in-depth process can be beneficial.
Calico for container security
At Tigera, we adopt various security strategies and frameworks, such as defense-in-depth, zero-trust, and the ATT&CK framework to design and develop products and features for containers and Kubernetes-based applications. A strong security team should utilize concepts from these frameworks and apply them across the entire organization to be successful. Calico as a container security solution offers many capabilities, all of which directly apply to one or more of the mitigating strategies that the ATT&CK framework recommends. The figure below is a list of current capabilities from Calico that can help mitigate against common attack techniques in a MITRE framework.
Reconnaissance tactics—ATT&CK framework
Now, let’s take a look at the first four tactics of the ATT&CK framework for containers. In part 2 of this blog series (coming soon), we will cover the rest of the tactics with additional coverage on key techniques that MITRE has ignored when it comes to container security, and how to address it.
Initial access
A threat actor is always looking for ways to enter the organization’s environment to move to the next steps. This initial access stage for containers can be done through scanning for any public-facing application that the organization has built. An example could be a web application with a form-fill and weak protection against SQL injection or cross-site scripting. Another example could be a container with weak credentials and SSH enabled. To have a public-facing application that is either prone to application-layer attacks or has easy login access is akin to leaving a key in the door.
Another reconnaissance method is waiting for developers to access any vulnerable container image placed in public repositories. Once the hacker knows someone has downloaded the image, they can use other tactics to gain access to the environment.
Calico’s granular, zero-trust runtime security features can mitigate this risk. These features include:
- Deep packet inspection
- Workload-centric web application firewall (WAF)
- Identity-based microsegmentation
- DNS policies
Read more about these features on Calico Cloud’s product page.
Execution
The next step an attacker will try to do is to execute some type of malicious code, spin up a new container, execute some code from the container orchestration platform, or get a user to unsuspectingly execute the code on the attacker’s behalf via social engineering (e.g., phishing campaigns using unsuspecting file extensions such as .doc). This stage is also part of the reconnaissance stage, where the attacker has not fully gotten access to the critical data or resources.
Calico’s deploy time security features can mitigate this risk. These features include:
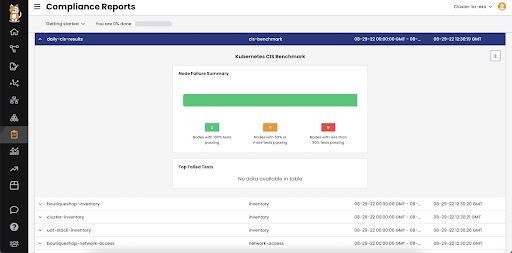
- CIS benchmark reports (KSPM)
- Identity-based microsegmentation
- DNS policies
Want to learn more about deploy time security? Check out our learn guide: Kubernetes Security: 8 Best Practices to Secure Your Cluster.
Persistence
A good quality for a sportsperson. But in this context, we are referring to the stage where a determined bad actor is trying to find alternate methods to infiltrate the organization’s network. Instead of placing a vulnerable image in a public registry, what if the attacker is placing the same vulnerable image in a private registry after gaining access to the registry itself due to weak credentials? This is a typical example of persistence—even though initial access has been a failure, continued attempts are made to gain access.
Calico’s deploy time security features can mitigate this risk. These features include:
- Calico Image Scanner
- CIS benchmark reports (KSPM)
- Identity-based microsegmentation
- DNS policies
Privilege escalation
This stage refers to the additional resources through which an adversary can introduce malware directly or further move to a different component in a container environment. Example techniques include escape to host, meaning that the adversary is trying to get to the underlying host on which Kubernetes or containers are hosted. Techniques under privilege escalation give the attacker a higher-level privilege (system, root) for a container or the host.
A combination of Calico’s build and deploy time security features can mitigate this risk. These features include:
- CIS benchmark reports (KSPM)
- Workload-based IDS/IPS (Intrusion Detection and Prevention)
- Global threat feed
To learn more about each of these Calico features and how the defense-in-depth approach can improve your organization’s security posture, see our container security solutions page. In my next blog, we will take a look at the rest of the matrix and how Calico’s solution provides a holistic approach with a zero-trust security model for containerized workloads.
Want to see how your organization fares in the zero-trust journey for cloud-native applications? Take our free Zero Trust for Cloud-Native Workloads Maturity Assessment to find out now.
Join our mailing list
Get updates on blog posts, workshops, certification programs, new releases, and more!


