As organizations transition from monolithic services in traditional data centers to microservices architecture in a public cloud, security becomes a bottleneck and causes delays in achieving business goals. Traditional security paradigms based on perimeter-driven firewalls do not scale for communication between workloads within the cluster and 3rd-party APIs outside the cluster. The traditional paradigm also does not provide granular access controls to the workloads and zero-trust architecture, leaving cloud-native applications with a larger attack surface.
Calico Cloud offers an easy 5-step process for fast-tracking your organization’s cloud-native application journey by making security a business enabler while mitigating risk.
Step 1: Visibility
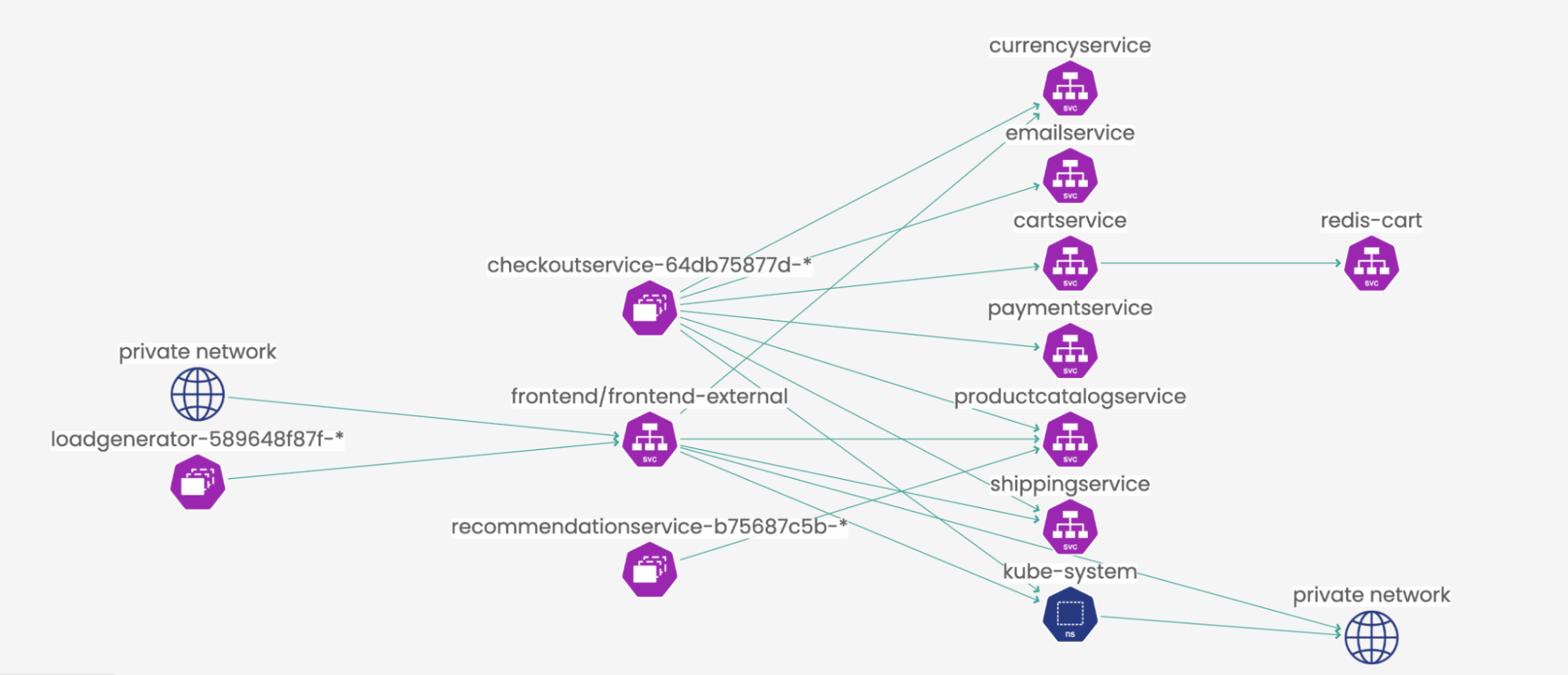
Gaining visibility into workload-to-workload communication with all metadata context intact is one of the biggest challenges when it comes to deploying microservices. You can’t apply security controls to what you can’t see. The traffic is not just flowing from a client to a server in this new cloud native distributed architecture but also between namespaces that reside between many nodes, causing flow proliferation. With Calico Cloud, you get a dynamic visualization of all traffic flowing through your network in an easy-to-read UI.
Example 1: You can view all the inside and outside (east-west and north-south) connections directly from Calico’s Dynamic Service and Threat graph. You can see in the image below that the private network is reaching out to the front-end of the storefront, and the frontend-external service is making east-to-west connections to other microservices (e.g., product catalog, shipping, etc.). You can also see that the checkout service is talking to the cart and payment microservices from the same page.
Read our Tutorial for more information about Calico’s Dynamic Service and Threat graph
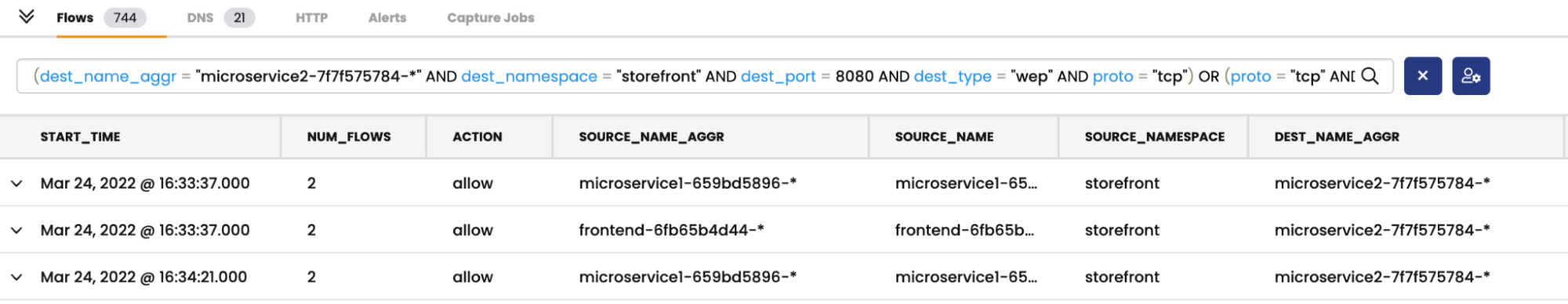
Example 2: The Dynamic Service and Threat graph allows you to double-click into individual flows, where you can see namespaces making connections, destination service, port number, number of flows, permit or deny, and various other information, including process names and IDs. This essentially provides a tailor-made, live view of your cluster and highlights any vulnerabilities and security gaps.
Step 2: Security Policies
After you see the security gaps, the next step is to build and apply security policies to have granular access control of the traffic flow in the environment. Calico Cloud provides a tier-based policy model with a high level of granularity for identity-aware microsegmentation (5-tuples and other identity-based elements like namespaces). Check out our website to learn more about security policies.
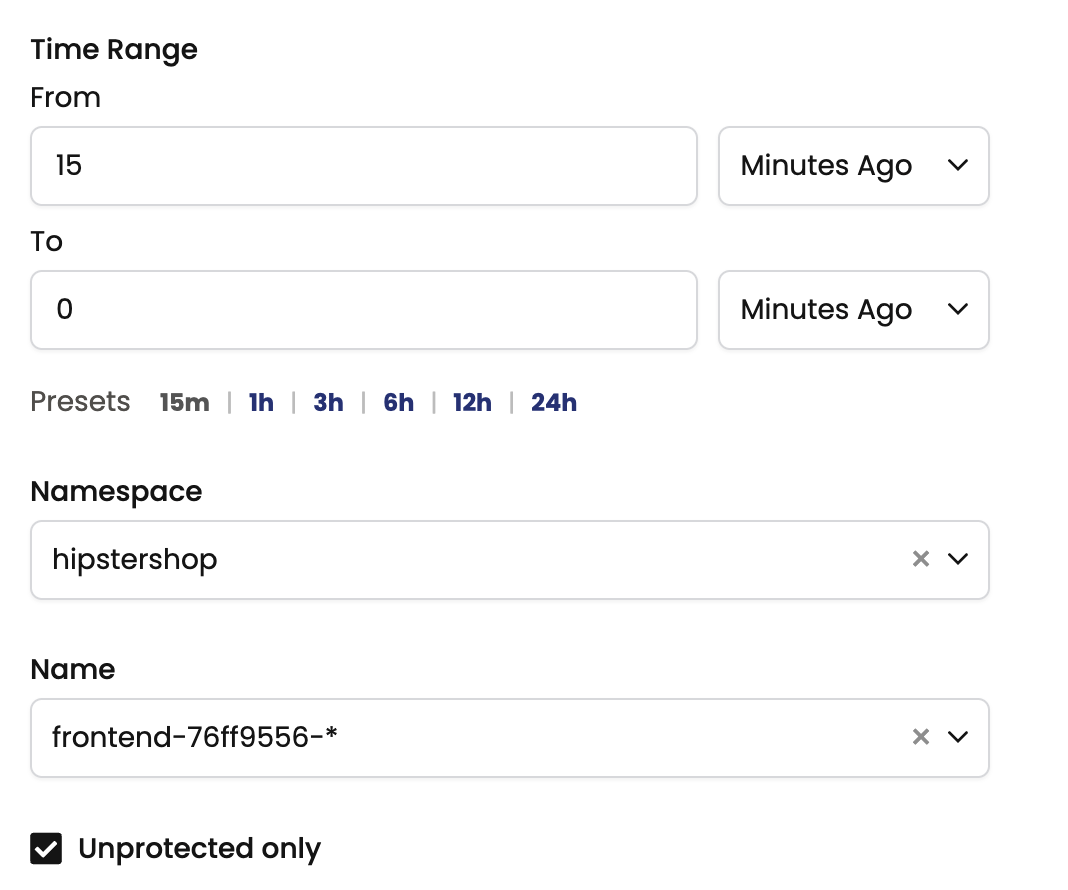
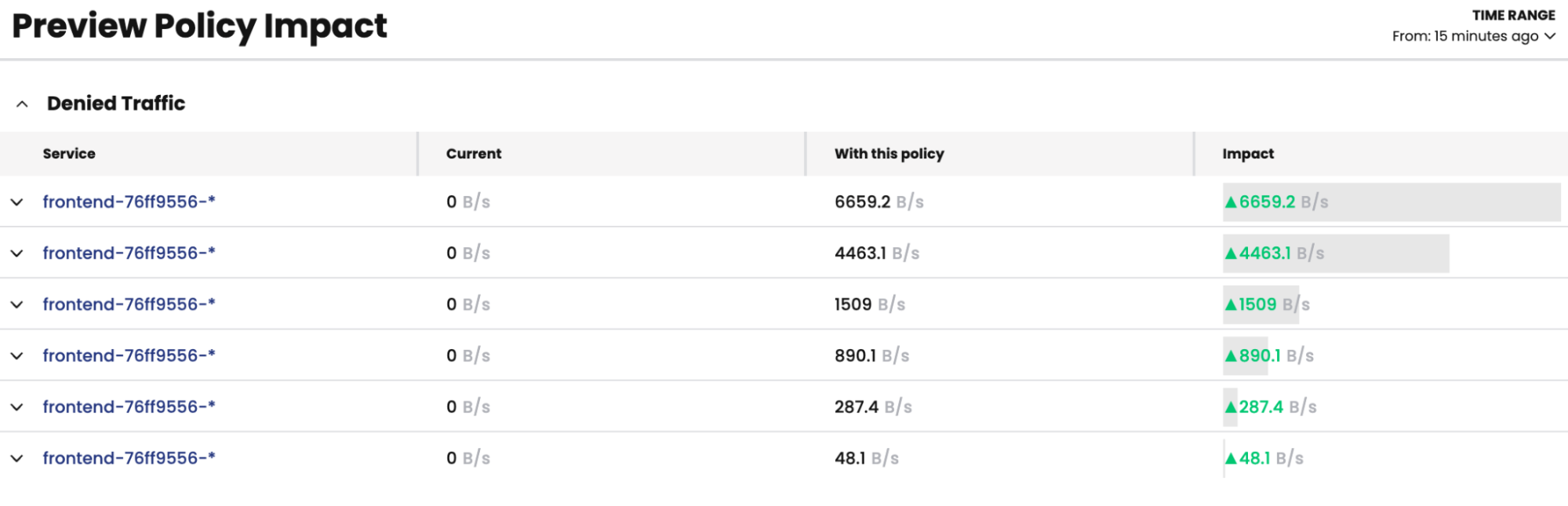
When you have more than a couple of microservices running in your environment, building security policies by hand can be a complex task. Calico Cloud offers a policy recommendation engine that you can use to build a base set of policies, and stage them to understand the impact of those security policies in your environment, thus automating the whole process of building security policies. The Security Policy Recommender can pull information for up to 24 hours and show you the granular recommendation per namespace.
Once you have the recommendation engine build out the granular policy, you can stage the policy and preview the flows that will be affected. A sample screenshot of all the frontend flows that will be affected is shown below.
Read more about Calico’s Security Policy Recommender
Step 3: Advanced Security Controls
Building a zero-trust architecture means having advanced security controls enabled as part of the architecture to identify zero-day threats in the environment. Here are a few examples of features that Calico Cloud offers today.
- FEODO tracker – Calico’s FEODO tracker lists all the command and control IP addresses in the cluster. You can automatically block those connections from going out of the pods (see below screenshot).
- Honeypods – Security admins can see if any suspicious connections exist in the environment by creating honeypods to check if any connections are being made to a pod.
- Data-in-transit encryption – Easily encrypt all traffic between pods using WireGuard, and avoid performance issues that come with TL
- Runtime threat defense – Calico Cloud provides an easy way to turn on advanced security features like workload-based IDS/IPS , anomaly detection, and WAF.
Step 4: Troubleshooting
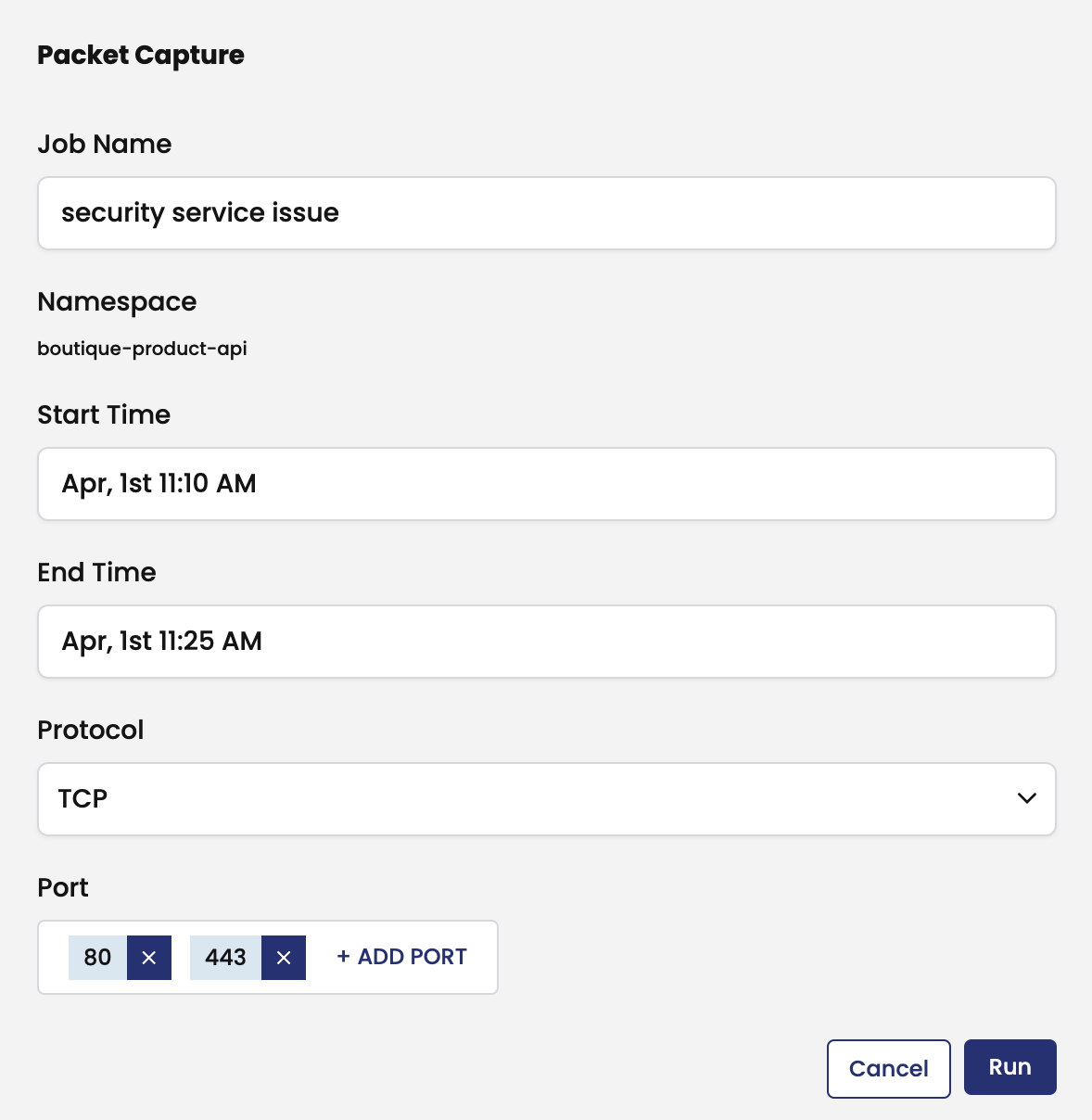
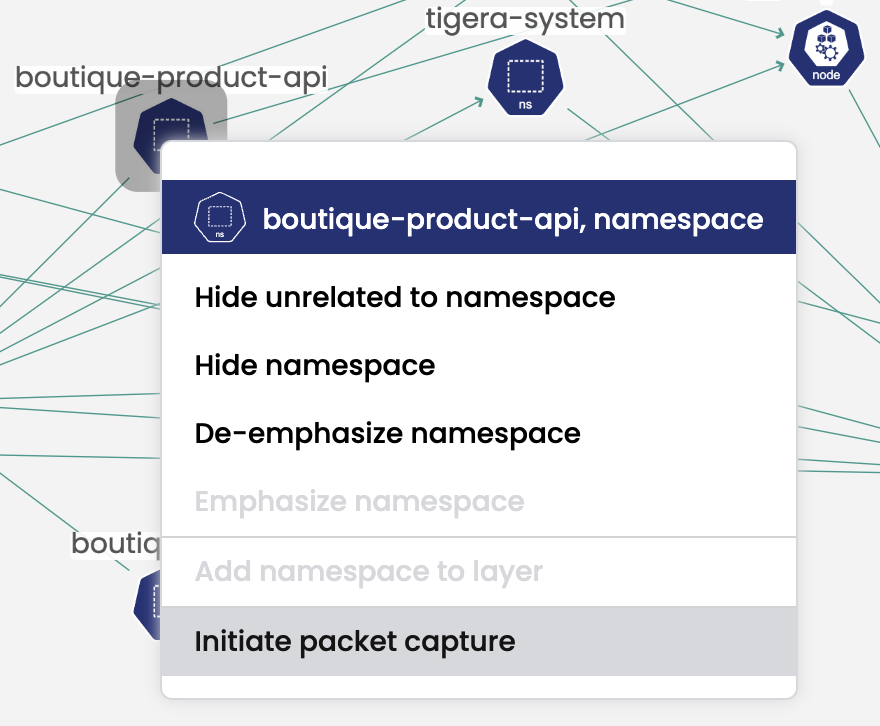
One of the challenges that the security team is always battling with ephemeral services is that issues don’t last long enough to troubleshoot. The Dynamic Packet capture capability in Calico Cloud provides an easy way to schedule the capture and download packet captures (pcap files) so you can identify and fix any issues in the environment.
Learn more about Dynamic Packet Capture
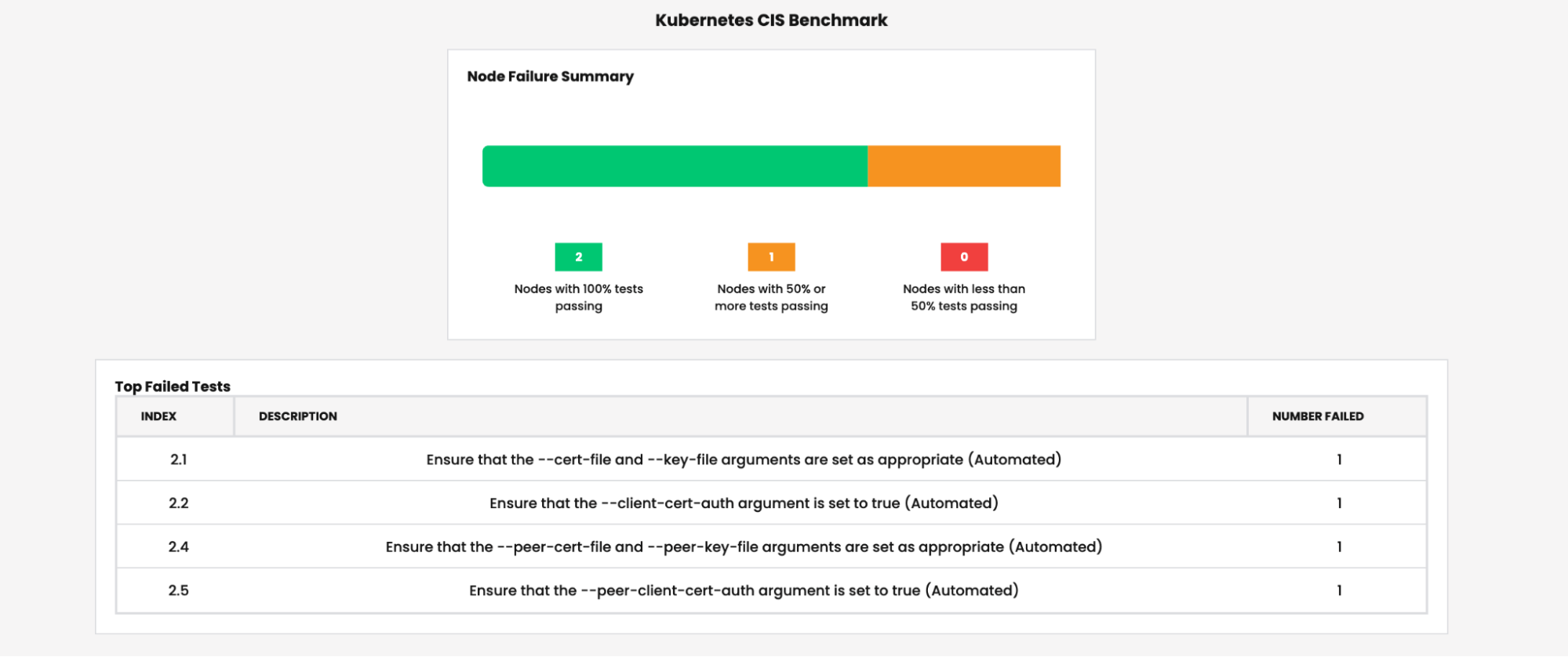
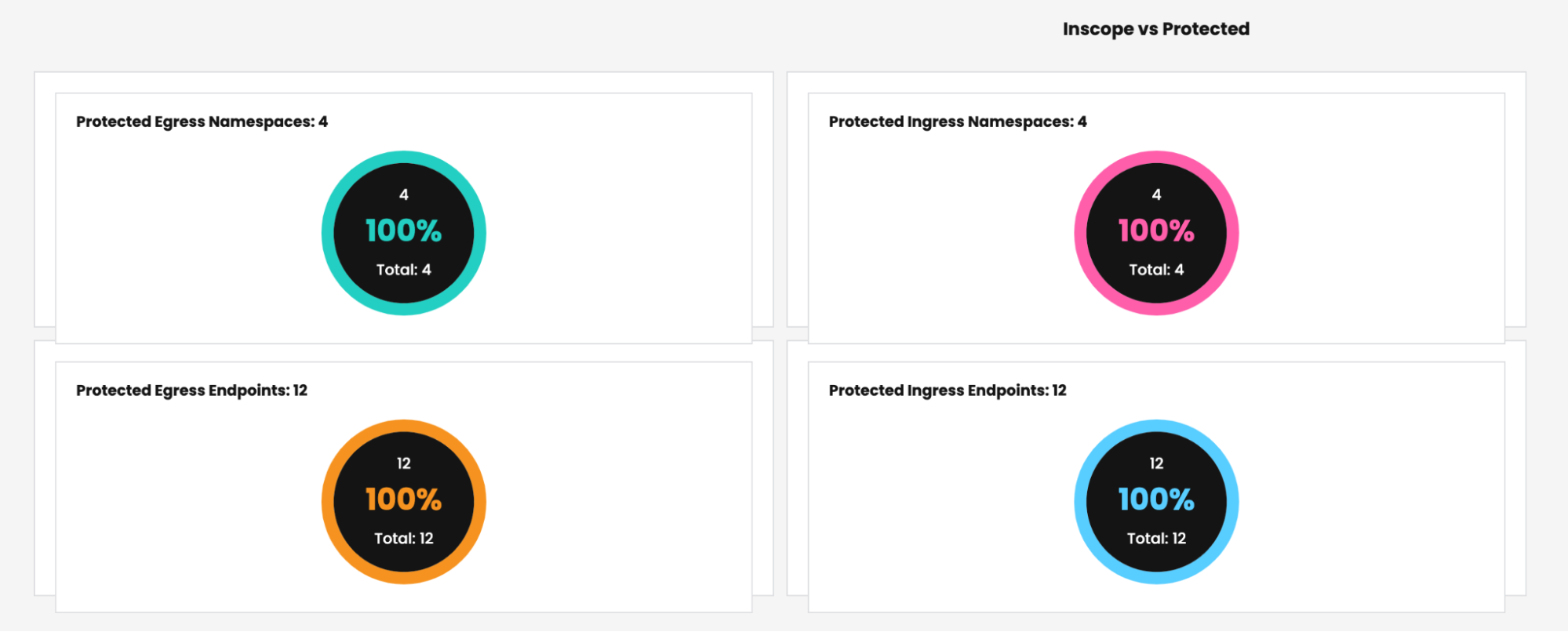
Step 5: Compliance Reporting
Calico Cloud compliance reporting provides an easy way to keep track of nodes and namespaces that are protected by ingress and egress rules. Organizations can easily download and share these with the compliance team to fast-track their cloud migrations. Organizations can also easily run benchmark reports against CIS standards for Kubernetes.
Learn more about Calico’s compliance and audit features.
Calico Cloud provides a lot of security features above and beyond what is listed here, but the goal of this post is to get you started on your Kubernetes journey so you have peace of mind around enabling security for workloads. This is not a comprehensive list of features that you will need, but is a great first step in applying security and moving from DevOps to DevSecOps on day 0. This will help you reduce time to deployment for your applications in a multi-cloud architecture.
Note: The above 5 steps can be easily tested with any Kubernetes cluster and Google’s Hipster Shop demo scripts. Try these features for yourself by signing up for a free trial of Calico Cloud.
Join our mailing list
Get updates on blog posts, workshops, certification programs, new releases, and more!